Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Protecting critical infrastructure means making sure important services like power, water, and transportation stay safe and keep working, even during trouble.
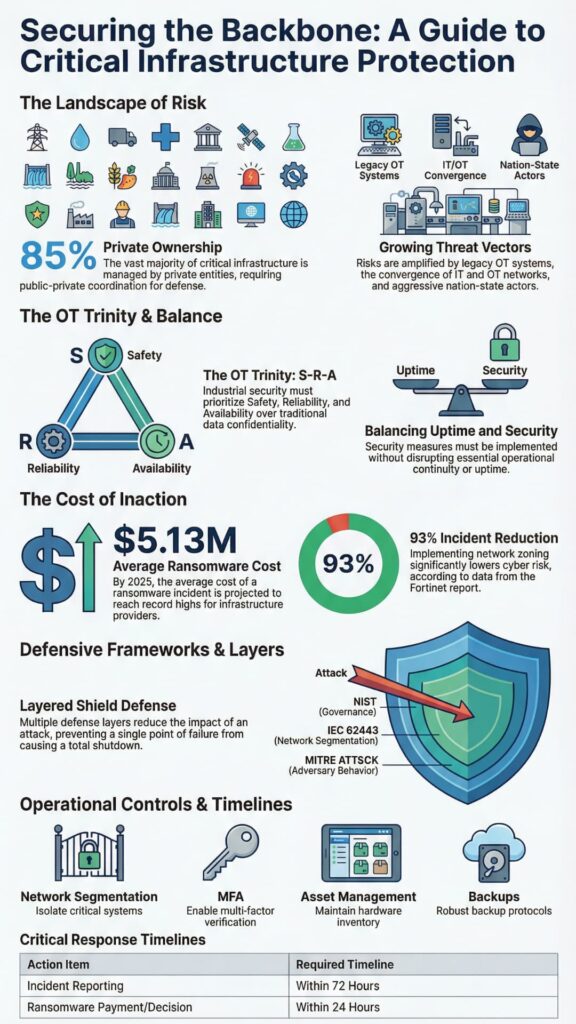
In the U.S., there are 16 key sectors that support daily life, and about 85% of them are owned by private companies, according to CISA.
When these systems fail, impacts spread quickly across communities and markets. We’ve worked inside these environments and seen how small gaps lead to major disruptions.
This guide focuses on what works, using real examples, trusted methods, and tested security tools. Keep reading to learn how real resilience is built.

Protecting critical infrastructure security means making sure important services stay safe and keep working, even when they are under attack. This includes power, water, transportation, healthcare, manufacturing, and government systems under CISA coordination.
Critical infrastructure protection goes beyond IT security. It also includes physical security and protecting operational technology and ICS systems, with clear rules that help everyone work together. In simple terms, this means keeping control systems and IT safe without interrupting daily work.
We’ve seen facilities where uptime goals quietly overruled security controls. Others went too far the opposite way and caused unsafe shutdowns. The discipline is in balance.
The Department of Homeland Security and other agencies say being ready is important because service outages can hurt people faster than stolen data.
Key Elements of the Scope:
Keep essential services running safely, even when systems are stressed, attacked, or degraded. Everything else supports that goal.
Aging systems, IT and OT convergence, and nation-state attackers have expanded the attack surface. Motivation has shifted from stealing data to disrupting operations. Oversight now sits with DHS and sector agencies, but the complexity keeps rising.
Many environments still run legacy OT, often decades old. Industry estimates suggest over 70% of OT assets use unsupported software or firmware. We regularly see controllers that cannot be safely scanned, patched, or logged. That reality drives every security decision.
Connecting systems made work easier, but it also gave attackers more ways to get in. The Colonial Pipeline attack showed that hackers can stop real-world services by breaking into computer systems.
Vulnerability drivers commonly include:
From our experience, decentralization cuts both ways. It is harder to take everything down at once, yet uneven security maturity leaves small sites exposed. Attackers know this. They aim for the weakest operational link.

The biggest risks today come from hackers and criminals trying to shut down important industrial systems. Their focus is disruption, safety impact, and coercion rather than espionage alone. Ransomware remains the most visible threat, with multi-day outages becoming the norm.
According to 2025 IBM/PurpleSec data, the average cost of a ransomware attack has reached $5.13 million, with critical sectors like healthcare and energy seeing significantly higher recovery premiums due to specialized downtime costs. These attacks often exploit poor segmentation and weak backups.
Nation state campaigns are quieter but more dangerous. Attackers slowly study systems, using stolen logins and trusted vendor access to move around. The MITRE ATT&CK for ICS shows how they can move between systems and control equipment in ways that put safety at risk.
The most consequential threat categories include:
Threat modeling in these sectors must assume patient adversaries. We plan defenses around impact, not intent. That mindset shift matters.
These frameworks show how to create rules, keep systems separate, find threats, and respond in ways that work for OT and real-world risks. Together they form a practical blueprint for critical infrastructure security.
The NIST Cybersecurity Framework organizes activity into six functions. Govern, Identify, Protect, Detect, Respond, and Recover.
Executives use it to align budgets and accountability. Operators use it to justify controls without harming uptime.
“The NIST CSF … provides a taxonomy of high-level cybersecurity outcomes that can be used by any organization … to better understand, assess, prioritize, and communicate its cybersecurity efforts.” – NIST Pubs [1]
IEC 62443 goes deeper into OT and ICS. It defines seven foundational requirements, including restricted data flow and timely response. In our field work, segmentation guided by IEC zones and conduits consistently reduced incident impact.
MITRE ATT&CK for ICS maps adversary behavior. It helps teams focus on the most important defenses based on how attackers really behave, not just on theory.
| Framework | Primary Focus | Core Strength |
| NIST CSF | Risk governance | Executive alignment |
| IEC 62443 | OT systems | Segmentation and safety |
| MITRE ATT&CK for ICS | Adversary behavior | Defense prioritization |
Used together, these frameworks help teams spot risks, fix problems, and handle incidents safely. According to NIST, risk based adoption improves consistency across IT and OT environments.

Keeping systems separate, letting only trusted people use them, knowing your devices, and using safe rules helps reduce damage and stop attacks from spreading. IEC 62443 FR5 emphasizes restricted data flow as a core safety control.
Network segmentation remains the most effective measure we deploy. Proper zoning between IT and OT, combined with firewalls and DMZs, prevents simple compromises from escalating.
According to Fortinet’s 2025 State of OT Report, organizations that moved from flat networks to unified networking and security platforms reported a 93% reduction in cyber incidents at remote OT sites.
Zero trust architecture extends this principle. Every user and device must verify continuously. In OT, this means:
Core protective strategies include:
At MSSP Security, we approach this pragmatically. We design controls that engineers accept and operators trust. Security that breaks processes does not last. Resilience does.
Watching systems often and practicing responses helps teams act fast. While industry benchmarks target containment within 48 hours, the 2026 CIRCIA mandate introduces a strict legal ‘clock’: covered entities must now report substantial incidents to CISA within 72 hours, and report any ransomware payments within 24 hours.
“CISA’s proposed rule would require a critical infrastructure company (a covered entity) to report to CISA within 72 hours after that entity experiences a substantial cyber incident (a covered event). Additionally, entities would need to report to CISA within 24 hours when they, or another party on their behalf, make a payment in response to a ransomware attack.” – congress.gov [2]
Detection in OT relies on behavior, not signatures. Intrusion detection tuned for industrial protocols spots deviations early. SIEM systems correlate events across IT and OT, reducing alert fatigue.
Response planning matters more than tooling. We have led tabletop exercises where untested plans failed under pressure. Facilities that practiced handling emergencies and recovery were able to get back to work faster and more safely.
Effective detection and response programs include:
The Cybersecurity and Infrastructure Security Agency says to store backups separately and practice manual operations so systems can keep working during ransomware attacks.
Using good security, tested backups, separated systems, and trained staff helps keep systems safe and running. Non compliance with NERC CIP can reach up to $1 million per day in penalties.
Balancing security and availability is cultural as much as technical. Operators prioritize safety. Security teams must respect that reality. Controls succeed when they reduce risk without adding fragility.
In our experience, the most successful programs start with fundamentals. They understand that some older systems can’t be fixed right away, so they protect them by keeping them separate and watching them closely.
| Practice | Security Outcome | Framework Alignment |
| Risk assessment | Prioritized controls | NIST Identify |
| Network zoning | Reduced spread | IEC 62443 |
| Offline backups | Ransomware recovery | CISA |
| Exercises | Faster response | NIST Respond |
Supporting practices include employee training, phishing defense, patch management, and clear governance policies. Over time, these measures build confidence across engineering and security teams.
Critical infrastructure protection (CIP) ensures that essential services such as energy, water, transportation, healthcare, and financial systems remain secure and reliable. It reduces cyber threats, physical risks, and operational failures that could disrupt daily life. Strong CIP supports public safety, economic stability, and national resilience by protecting the systems people depend on every day.
Organizations should begin with thorough risk assessment, threat modeling, and vulnerability management to identify weaknesses. They should use penetration testing, security audits, and asset management to understand exposure. Risk mitigation strategies such as patch management, network segmentation, and access control reduce the likelihood and impact of cyber threats.
OT security depends on network segmentation, intrusion detection, firewall configuration, and secure remote access. ICS protection also includes monitoring SCADA systems, applying encryption protocols, and enforcing multi-factor authentication. A zero trust architecture limits system access, while endpoint protection and patch management reduce attack surfaces across industrial control systems.
Organizations should establish a clear incident response plan supported by trained teams and tested disaster recovery procedures. They should use SIEM systems, threat intelligence, and forensic investigation to detect, analyze, and contain attacks. Resilience planning, ransomware mitigation, and data loss prevention ensure that services recover quickly and continue operating during cyber disruptions.
Regulatory compliance helps organizations follow proven security practices using the NIST framework, CISA guidelines, and DHS directives. These standards support governance policies, risk mitigation, and security audits. They also guide physical security, supply chain security, and resilience planning across energy, water, transportation, healthcare, and government critical infrastructure sectors.
Protecting critical infrastructure means using several safety tools, knowing real dangers, and making sure security fits everyday work.
The best results come when organizations improve safety all the time, not just once. Frameworks guide the work, but people sustain it.
As systems like energy, water, transportation, and smart cities become more connected, the cost of doing nothing gets higher. The way forward is clear, practical, and possible with the right partners and priorities.
Join our experts to streamline your security operations, reduce tool sprawl, and build a resilient, high-performing security stack that aligns with your business goals.