Your security team is drowning in alerts. Every ping is a potential crisis, but most are just noise. This is the reality for businesses in Fullerton and across Orange County, where the volume of threats outpaces the capacity of human analysts. The solution isn’t just more staff; it’s smarter processes.
Security Orchestration, Automation, and Response (SOAR) implementation consulting provides the blueprint to turn that chaos into a coordinated, automated defense. It connects your disparate security tools, automates repetitive tasks, and ensures your team focuses on genuine threats.
We’ve seen it cut response times by more than half. Keep reading to understand how a structured SOAR engagement can secure your operations and give your team their focus back.
Key Takeaways
- SOAR integrates your security tools into a single, automated workflow.
- Custom playbooks automate responses to common threats like phishing and ransomware.
- Expert consulting ensures a smooth deployment tailored to your specific needs.
The Overwhelming Tide of Security Alerts
It usually starts quietly. One alert pings on the screen. Then ten more. By the end of the day, your Security Operations Center (SOC) is drowning in thousands of notifications.
The real issue isn’t only the volume, it’s the lack of connection between them. Your firewall logs sit in one place, endpoint protection data in another, email security alerts in yet another. None of them talk to each other in a meaningful way. So each alert feels isolated, stripped of context.
When that happens:
- Analysts spend more time sifting than thinking
- Noise starts to blur into the background
- Critical threats blend in with low-risk events
That’s how alert fatigue sets in. The mind just stops reacting to the constant stream, and dangerous signals get missed. For a mid-sized tech firm in Fullerton, this isn’t some abstract security theory. It’s a steady, daily drag on people, time, and attention, while risk quietly grows in the background [1].
A strong security program shouldn’t chase “more data” as its main goal. It should chase clarity, knowing what matters, when it matters, and why.
SOAR as Your Security Nervous System
SOAR implementation steps into this mess and works like a central nervous system for all your security tools. Instead of treating alerts as scattered messages, it pulls them into one coordinated response system.
Here’s what it actually does:
- Ingests alerts from your SIEM
- Connects to cloud platforms and services
- Pulls in data from threat intelligence feeds
- Correlates alerts across different tools
From there, SOAR uses predefined logic and playbooks to:
- Sort alerts based on risk and relevance
- Prioritize what analysts should look at first
- Trigger automated responses for known or low-complexity threats
This kind of setup doesn’t push humans out of the loop. It does the opposite. It frees your analysts from repetitive triage work, so they can:
- Investigate complex attack paths
- Fine-tune detection rules
- Focus on high-impact incidents
SOAR doesn’t replace your team’s judgment. It gives them room to actually use it.
What SOAR Implementation Consulting Actually Does

So, what does a SOAR consultant do? They don’t just install software. They begin with a deep assessment of your current security posture. This gap analysis looks at your tools, your processes, and your team’s skills. They identify where manual tasks are creating bottlenecks.
For instance, a simple phishing email might require an analyst to manually check five different databases. A consultant designs a playbook that automates those five checks in seconds, leveraging the power of security orchestration automation to streamline workflows and reduce human error.
The process is typically phased. It’s a journey from assessment to optimization.
- Security Posture Assessment: Evaluating tools, processes, and policies.
- Playbook Development: Designing automated workflows for common incidents.
- Integration & Deployment: Connecting SOAR to your existing security ecosystem.
- Training & Knowledge Transfer: Empowering your team to manage the system.
- Ongoing Optimization: Continuously refining playbooks against new threats.
This structured approach ensures the solution fits your business, not the other way around. The consultant’s role is to be a guide, translating complex security needs into an efficient, automated reality.
| Phase | What It Includes | Outcome for Your Team |
| Security Posture Assessment | Review of tools, processes, policies and skills | Clear view of gaps and priorities |
| Playbook Development | Design of automated workflows for common incidents | Faster and consistent response actions |
| Integration and Deployment | Connecting SOAR to SIEM, EDR, cloud and email tools | Unified workflow that reduces manual work |
| Training and Knowledge Transfer | Hands on sessions and documentation | Team can operate and modify SOAR confidently |
| Ongoing Optimization | Continuous tuning against new threats | Stronger automation accuracy over time |
The Tangible Benefits for Your Fullerton Business

You can almost feel the difference when a security team moves from reacting to actually staying ahead. That shift is where a solid SOAR platform proves its worth, not in theory, but in minutes saved and mistakes avoided. For most Fullerton businesses, the impact shows up in two main areas: time and accuracy.
Faster Response When It Matters Most One of the clearest numbers to watch is Mean Time to Respond (MTTR). That’s how long it takes your team to go from alert to action. With SOAR, a big chunk of the early work gets automated, such as data enrichment and initial triage.
This is exactly where a managed SOAR platform can deliver consistent and measurable improvements in efficiency and response times. For most Fullerton businesses, the impact shows up in two main areas: time and accuracy.
Faster Response When It Matters Most
One of the clearest numbers to watch is Mean Time to Respond (MTTR). That’s how long it takes your team to go from alert to action.
With SOAR, a big chunk of the early work gets automated, such as:
- Data enrichment (pulling user, host, and IP details automatically)
- Initial triage (sorting alerts into high, medium, or low priority)
- Routine checks (like reputation lookups or basic correlation)
When those steps run on their own, MTTR can drop by 50% or more. That’s not a small quality-of-life gain, that’s the difference between:
- A ransomware attempt being contained in a few minutes
- Or spreading through key systems for hours
For a hospital, clinic, or bank in Orange County, that speed can protect patient records, transaction data, and even daily operations.
Consistency You Can Prove
Speed helps, but consistency is what builds trust in the process. Manual workflows, especially under stress, leave room for:
- Skipped steps
- Missed evidence
- Incomplete documentation
SOAR uses automated playbooks so every incident follows a set, documented path. That means:
- Each case is handled according to best practices
- Actions are logged in detail
- Reviews and audits become much easier
This structure supports compliance with frameworks and regulations such as:
- NIST
- GDPR
- Industry-specific policies or internal security standards
You’re not just saying you follow a process, you can actually show it.
Better Work for Your Security Team
There’s also a human side here. When analysts spend most of the day clearing false positives or repeating the same checks, their skills stall out. SOAR helps shift their focus toward:
- Deep-dive investigations
- Complex threat hunting
- Improving detection rules and response playbooks
So the return on investment isn’t only about avoiding breaches or cutting losses. You end up with:
- A sharper, more engaged security team
- Less burnout from constant noise
- More energy spent on strategy instead of busywork
For a Fullerton business trying to stay secure without burning out its staff, that might be the most valuable change of all.
| Benefit Area | Manual Process Impact | With SOAR Implementation |
| Response Time (MTTR) | Hours spent on enrichment and triage | Reduction of 50 percent or more |
| Analyst Workload | Repeated manual checks and validation | Automated triage frees analysts for threat hunting |
| Consistency | Error prone steps under pressure | Standardized responses using automated playbooks |
| Compliance | Hard to maintain repeatable evidence | Playbooks enforce best practice and documentation |
Choosing the Right Consulting Partner
You can usually tell pretty quickly whether a security consultant is there to help you, or just to sell you a product. That difference matters a lot when you’re picking a partner for SOAR implementation.
The truth is, not every consulting service works the same way. Some are tied closely to one vendor, while others stay more independent. That’s where you want to be careful.
What to Look For in a SOAR Partner
When you’re evaluating a SOAR consulting partner, a few traits stand out as non-negotiable:
- Vendor-agnostic guidance
They shouldn’t push a single platform just because they have a partnership. The right tool for a nearby company might not fit your systems, your size, or your team. - Environment-first assessment
A strong consultant will start by understanding:
- Your current security stack
- Existing integrations (SIEM, EDR, email, cloud)
- Your team’s skills and internal workflows
- Platform recommendation based on fit
Only after that should they recommend tools such as:
- Palo Alto Cortex XSOAR
- Splunk SOAR
- Or another platform that fits your setup and budget
- Clear, concrete deliverables
You should see a detailed plan that includes:
- Designed and configured playbooks
- Documented workflows and processes
- Training sessions for your team
- Handover documentation so you’re not dependent on them forever
This kind of structure keeps the project grounded and measurable.
Why a Regional Partner Helps Fullerton Organizations
For businesses in Fullerton and the broader Orange County area, there’s a strong case for working with a regional consultant instead of someone completely remote.
A local or regional partner usually:
- Understands the local business environment and regulations
- Knows common challenges in sectors like healthcare, education, tech, and finance
- Can offer more in-person workshops, working sessions, and onsite tuning
That proximity helps when your team needs:
- Hands-on help during rollout
- Fast feedback loops while playbooks are being tested
- Support during real incidents, not just during planning meetings
Over time, the right consultant starts to function like an extension of your internal security team. They’re not just focused on turning the tool on, they’re watching how well it’s actually used.
That includes:
- Helping your analysts feel confident using SOAR daily
- Adjusting playbooks based on real incidents
- Tracking your growth in security maturity, not just license usage
The goal isn’t to have SOAR sitting on a slide deck or as another unused tool. The real win is when your people use it well, and your security operations feel sharper, calmer, and more under control because of it.
The Human Element: Aligning Your Team with SOAR
You can almost feel the tension when a new automation tool gets announced. Some people lean in with curiosity, others lean back with worry. That mix of reactions is normal, especially in a SOC where work already feels intense. A common fear is simple: “Is this going to replace me?”
With SOAR, the reality is more layered than that. It doesn’t erase the need for skilled analysts, it shifts where their time and attention go. The key is to have strong outsourced security automation consulting that aligns people and technology, helping your team use automated processes without losing their critical judgment or control over security operations.
A common fear is simple: “Is this going to replace me?” With SOAR, the reality is more layered than that. It doesn’t erase the need for skilled analysts, it shifts where their time and attention go.
What SOAR Changes , and What It Doesn’t
SOAR is best at the work humans usually dislike but still have to do, such as:
- Repetitive data gathering across multiple tools
- Low-level triage and classification
- Running the same checks over and over on similar alerts
When those tasks are automated, your analysts can put their energy into:
- Critical thinking and pattern recognition
- Deep-dive investigations into real threats
- Strategic decision-making and process improvement
We’ve seen SOC teams move from:
- Being overloaded “ticket closers”
- To acting more like proactive threat hunters
That kind of shift doesn’t happen by accident, though. It needs clear communication and good change management. People need to hear, directly and honestly, that:
- The SOAR platform is there to assist them
- It handles grunt work, not creativity or judgment
- Their expertise is still central to protecting the business
When the message is right, SOAR feels less like a threat and more like a strong extra pair of hands.
Aligning People and Automation Through Consulting
Credits : IBM Technology
Good consulting in this space isn’t just wiring up tools and walking away. It should focus heavily on aligning human talent with the new technology.
That usually includes:
- Comprehensive training programs
- Hands-on sessions, not just slide decks
- Real-world use cases based on your own alerts and incidents
- SOC team upskilling
Analysts learn how to:- Create and adjust playbooks
- Read and interpret automated workflows
- Decide when to override or step into a process
- Clear roles and expectations
Everyone understands:- Which tasks are automated by default
- Where human approval is required
- How to escalate when something looks unusual
The deployments that work best are the ones where analysts feel:
- More capable, not sidelined
- More in control of the process, not confused by it
- More protected from burnout, because the machine handles the repetition
When technology and talent grow together, the SOC starts to feel different. Less reactive, more steady. Automation handles the noise, your people handle the judgment. And that balance is where security operations become both efficient and resilient [2].
FAQ
How do SOAR implementation consulting services in Fullerton help my team improve daily work?
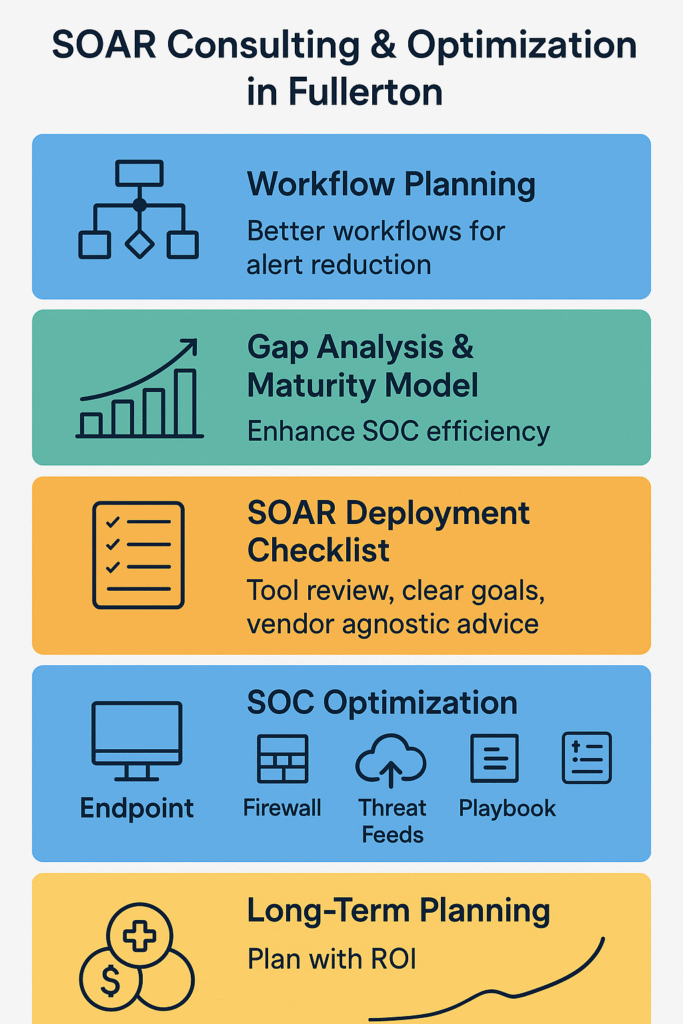
SOAR implementation consulting services in Fullerton help you plan better workflows. You get support with security orchestration automation response, incident response automation, threat detection integration, and SIEM SOAR connector setup. Consultants use gap analysis cybersecurity and the SOAR maturity model to find weak spots. This helps reduce alert fatigue and improve mean time to response reduction for your team.
What should I check before starting a cybersecurity SOAR deployment for my company?
You should look at your current tools and goals. A cybersecurity SOAR deployment needs clear requirements planning security and good resource management SOAR steps. You can review SOAR vendor selection options and get vendor agnostic advice. Many teams in Fullerton use playbook assessment services and SOAR playbook development to build strong plans before they go live.
How can Fullerton SOC optimization improve automated incident response in my environment?
Fullerton SOC optimization helps you use automated incident response in a practical way. You can add endpoint integration SOAR, firewall orchestration tools, and threat intelligence feeds. Teams also use phishing response automation and ransomware playbook design to cover common attacks. This work improves SOC efficiency consulting efforts and supports NIST compliance SOAR activities across your environment.
What skills do we need for cloud SOAR deployment or on-premise SOAR setup projects?
You need people who understand custom API integrations, workflow automation consulting, and performance tuning SOAR tasks. Many teams add SOAR training programs and SOC team upskilling to help staff grow. Southern California SOAR consultants also support stress testing playbooks and continuous playbook maintenance. These steps help with human capital alignment and talent alignment cybersecurity work.
How do Orange County SOAR experts improve long term planning for mid-sized businesses?
Orange County SOAR experts guide teams through strategic security planning. They help with organizational security alignment and business process management. They support phased rollout strategy plans and ROI SOAR calculation. Many mid-sized business SOAR projects include healthcare incident response needs, finance SOAR solutions, and LA area security operations. These steps give leaders better decision support cybersecurity data.
Your Path to a Calmer Security Future
Your team moves forward when you accept that manual security operations no longer scale. SOAR helps you shift from reacting to shaping your defense. You cut noise. You regain control. You focus on real risks. Start by reviewing your gaps. Set clear automation goals. Work with specialists who design solutions that match your environment.
You get guidance that covers needs analysis, vendor selection, PoC support, and integration planning. You improve visibility. You reduce tool sprawl. You strengthen your service quality with support backed by 15 years of experience and more than 48,000 completed projects.
Take your next step and join the experts at MSSP Security.
References
- https://research-journal.org/en/archive/10-124-2022-october/10.23670/IRJ.2022.124.8
- https://www.digitalsecurityforensics.org/digisecforensics/article/view/45
