Choosing managed WAF provider in Fullerton isn’t about buying another tool, it’s about finding a team that keeps protection working every single day. We see it all the time: alerts stack up, rules never get tuned, and attackers find the gaps anyway. The software isn’t the hard part.
The hard part is the ongoing work, reviewing traffic, stopping false positives, adjusting policies, and responding fast when things change. At MSSP Security, we’ve helped providers sort through this for years, and it always comes back to operational discipline, not sales talk. Keep reading to see what matters most.
Key Takeaways
- Managed WAF success depends more on tuning, monitoring, and response than on the underlying engine.
- Fullerton businesses benefit from combining cloud-scale protection with local operational support.
- Compliance, false-positive reduction, and clear SLAs matter more than feature checklists.
What is a Managed WAF and Why does it Matter for Fullerton Businesses?
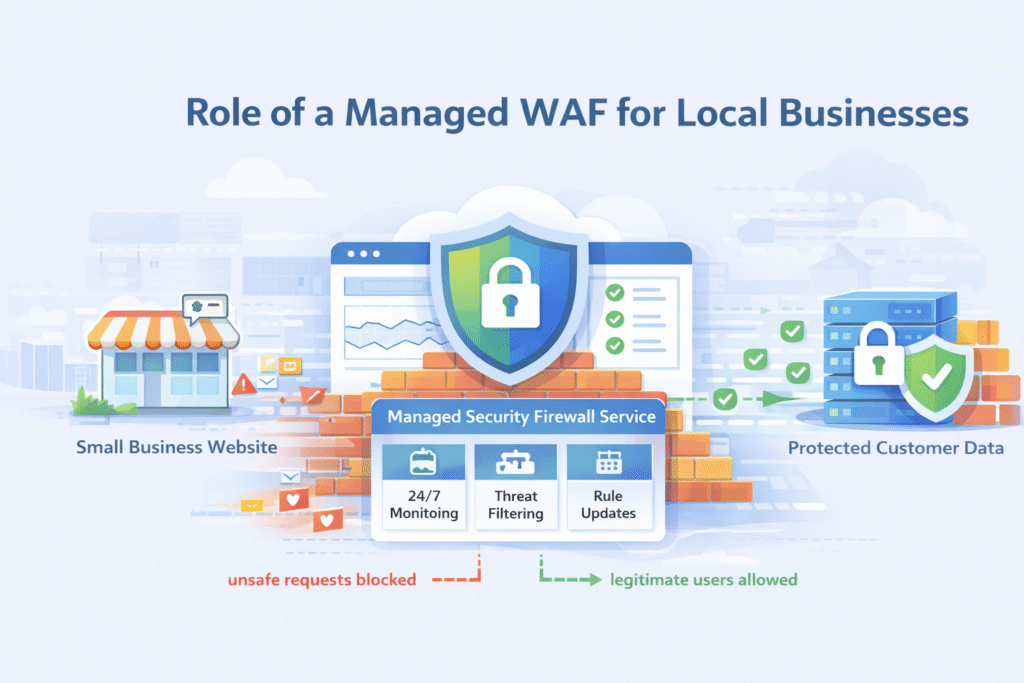
A managed Web Application Firewall filters malicious traffic while experts handle tuning and response. It reduces risk for local businesses facing automated attacks and compliance pressure.Here’s the simple version: a WAF sits in front of our apps and checks all the traffic coming in.
The “managed” part is the people. We’ve seen it happen over and over. A company buys a great WAF, but then they’re stuck. No one knows how to tune the rules, and alerts just go ignored. That is why a managed Web Application Firewall (WAF) matters most when it includes real operational support, not just software.
According to OWASP, over 70% of common web attacks fall into categories like SQL injection and cross-site scripting. Blocking them sounds easy on paper, but real-world traffic is messy.
A managed approach matters because it gives us:
- Continuous tuning of OWASP rules to cut down on false alarms.
- 24/7 monitoring with actual incident response.
- Ongoing adjustments as our apps grow or change.
From our perspective, most organizations don’t fail because of bad tools. They fail from a lack of sustained, knowledgeable attention. That’s the exact gap a good managed service is built to fill.
Which Security Threats should a Managed WAF Cover by Default?
Credits: Definer
A strong managed WAF should block OWASP Top 10 risks, DDoS floods, bots, and zero-day exploits with continuous rule updates.
Attacks today are rarely just one thing. What we see in practice is a blend, credential stuffing mixed with bot traffic and API probing, all happening at once.
The good services combine signature filtering, anomaly detection, and threat intelligence to get smarter over time, especially when paired with outsourced cybersecurity threat hunting in Fullerton that helps uncover patterns beyond basic rule sets.
At a minimum, our managed WAF should handle:
- SQL injection and cross-site scripting (XSS) for dynamic apps.
- Bot mitigation to stop scraping and automated abuse.
- Rate limiting and challenge mechanisms for suspicious traffic.
- API security for mobile and SaaS backends.
- Integration with DDoS scrubbing for big floods.
We always remind our clients: a WAF isn’t a magic shield. Without proper tuning, basic filtering can break our apps or miss real threats. The good services combine signature filtering, anomaly detection, and threat intelligence to get smarter over time.
Which Security Threats Should a Managed WAF Cover by Default?
It needs to handle the usual suspects, plus the blended attacks that are common now. Attacks today don’t come one at a time. We see credential-stuffing bots, mixed with API probing, followed by a Layer 7 DDoS surge, all in the same hour. Research reported that in 2023, the average large-scale DDoS attack was over 800 Gbps. The volume is staggering.
A solid baseline for a managed service should cover:
- The core OWASP Top 10, like SQL injection and cross-site scripting.
- Bot mitigation to stop scrapers and automated abuse.
- Rate limiting and challenges to slow down attackers.
- Security for our APIs, which are a huge target now.
- Integration with DDoS scrubbing for the big flood events.
We always tell our clients: a WAF isn’t a set-it-and-forget-it shield. Relying only on pre-set signatures can break our app or miss clever attacks. The good services mix signature filtering, behavior analysis, and live threat intel. That combo is what actually improves accuracy over time.
How Important is Local Fullerton or Orange County Presence?
The cloud handles the traffic, but local presence handles the panic. Yes, WAF traffic is processed in global data centers for speed. But when something goes wrong, having someone who understands our local business context, and can drive over if needed, brings a different kind of peace of mind.
Studies suggest on-site support can cut incident resolution time by about 30%, especially during complex, multi-system outages. We’ve sat in rooms with local IT teams from Fullerton companies during incident reviews. That face-to-face troubleshooting is invaluable.
Local familiarity helps with:
- Navigating California’s specific compliance expectations.
- Coordinating directly with our internal IT lead or executives.
- Supporting hybrid setups where some apps are still on-premise and latency is a real concern.
In our experience, the best outcomes blend the power of a global cloud WAF with the hands-on, contextual knowledge of a team that knows the Orange County landscape.
What Compliance and Regulatory Requirements Should be Supported?
It has to check the boxes for the auditors, clearly and without extra hassle. For Fullerton businesses in retail, healthcare, or fintech, compliance isn’t a suggestion. It’s mandatory. The PCI Security Standards Council notes that non-compliance fines can hit $100,000 per month. That gets a CFO’s attention fast.
“A properly configured WAF that is regularly updated becomes a central compliance enabler under PCI DSS 4.0. WAFs meet these criteria by offering real-time protection, audit log generation, and policy enforcement tailored to PCI DSS requirements.” – Indusface [1]
A managed WAF service should directly support:
- PCI-DSS requirements for web application firewalls, with clear documentation.
- Audit-ready logging and reports for standards like SOC 2.
- Protocols for handling data under HIPAA or state laws like CCPA/CPRA.
- Straightforward evidence for proving due diligence during an audit.
We advise our MSSP partners to ask very practical questions: How are compliance reports generated? How long are logs kept? Is this evidence part of the service, or an extra charge? Getting clear answers upfront prevents a world of stress later.
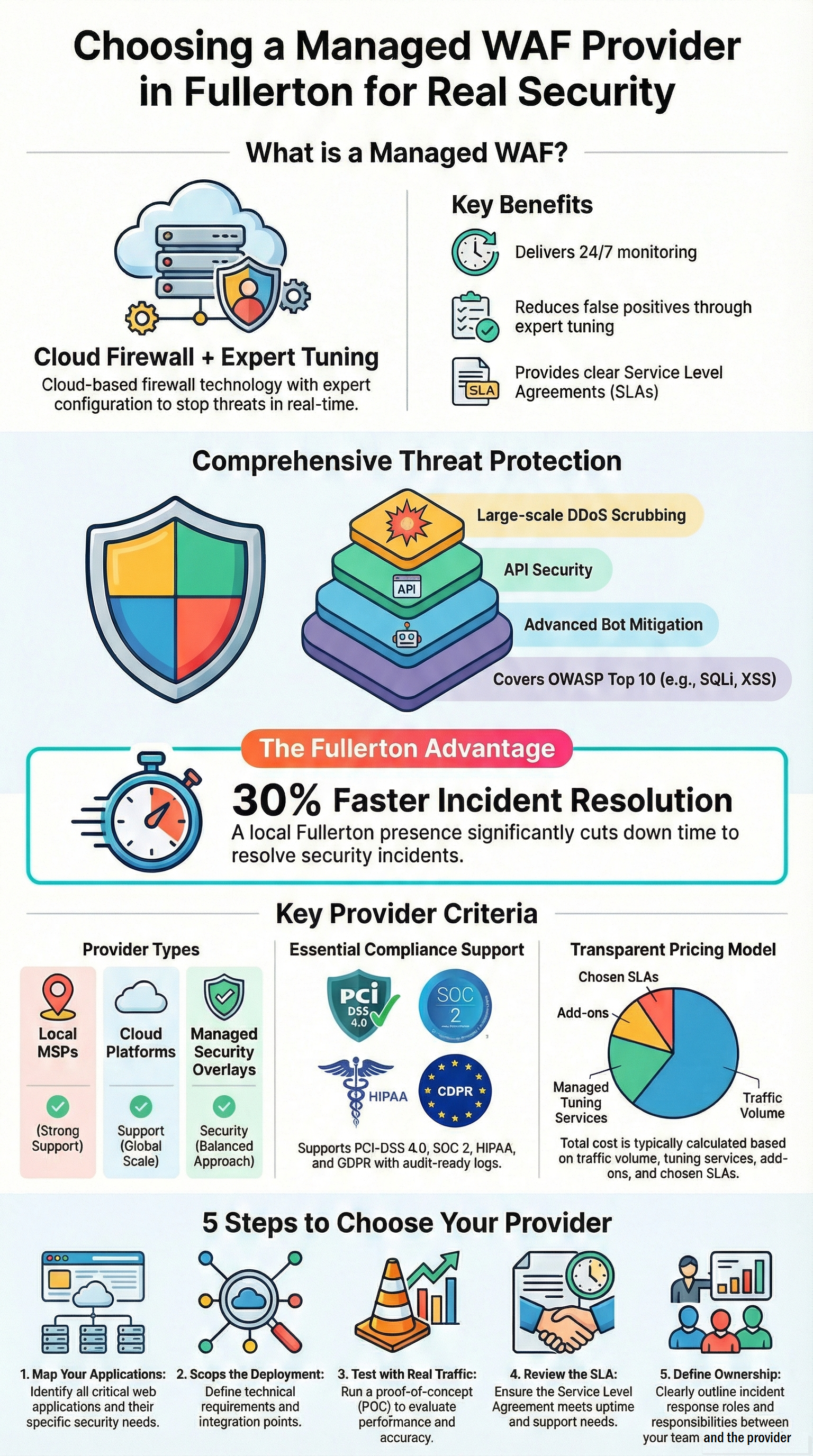
How do Pricing Models Compare For Managed WAF Services?
The sticker price is often just the beginning. Pricing can be confusing. A platform like AWS WAF might list a base cost of $0.60 per million requests. But that’s just for the platform processing the traffic. It doesn’t include the salary of a security engineer to tune it, monitor it, and respond to alerts at 2 a.m.
Here’s a breakdown of what we’re really paying for:
| Cost Component | What It Covers | Why It Matters |
| Traffic Volume | The number of requests inspected. | Costs can spike if our app traffic grows quickly. |
| Managed Services | The human work: tuning, monitoring, incident response. | This is what reduces false positives and downtime. |
| Add-on Protections | Extra layers for bots, APIs, or advanced DDoS. | Improves our overall resilience. |
| SLAs | Guarantees for uptime and response times. | This protects our revenue and customer trust. |
We’ve seen the “cheapest” option become the most expensive after a single outage blocks customers. It’s smarter to evaluate the total operational cost, not just the line item on the bill.
Which Local Managed IT Providers Serve Fullerton Businesses?
There are familiar names here that combine IT support with security. About 60% of small and midsize businesses outsource their security operations, it’s just too hard to hire for. In Fullerton, several regional IT providers offer managed services that include firewall and security management.
Firms are often in the conversation. They typically provide WAF capabilities through partnerships with larger cloud platforms or security vendors.
When local businesses evaluate them, they usually focus on:
- How deep their managed security offerings really go.
- Whether they can support a mix of cloud and on-premise systems.
- Getting reliable after-hours and emergency support.
What we often recommend is a layered approach: use a local MSP for hands-on IT support, and pair them with a specialized managed security provider to ensure the WAF gets the dedicated, expert attention it needs.
What Advantages do National or Global Managed WAF Platforms Offer?
They bring massive scale and threat intelligence that’s hard to match. The global WAF market is growing fast, over 15% a year, fueled by cloud adoption. Platforms like Imperva, Microsoft Azure WAF, and Cloudflare have a huge advantage: they see attack patterns from across the globe and can update their defenses in near real-time.
“Managed rules are written by security experts who have extensive and up-to-date knowledge of threats and vulnerabilities based on threats observed across many customers [allowing you to] quickly get started with AWS WAF rules for your application.” – AWS Marketplace [2]
These big platforms excel at:
- Soaking up massive, distributed DDoS attacks that would overwhelm smaller systems.
- Sharing threat intelligence learned from thousands of other companies.
- Seamlessly supporting apps deployed across multiple clouds or regions.
The catch? These platforms often expect we to manage the fine-tuning ourselves, or they sell that as a separate, expensive service. Many Fullerton companies we work with use these powerful global platforms, but then partner with a managed security service to handle the operations and emergency response.
How do Leading Providers Compare For Fullerton Use Cases?
It comes down to the blend of local touch and global muscle. Most WAF providers promise 99.99% uptime. But high availability doesn’t automatically mean we’re well-protected. An enterprise platform like Imperva is powerful, but its complexity can be overwhelming without expert management.
Here’s a quick comparison of the common models:
| Evaluation Factor | Local MSP Model | Cloud-Only WAF Platform | Managed Security Overlay |
| Local, hands-on support | Strong | Very Limited | Moderate to Strong |
| Global scale & threat intel | Limited | Very Strong | Strong (via the platform) |
| False positive reduction | Variable, depends on skill | Our problem to solve | Their core service |
| Compliance reporting | Usually included | Often an add-on | Typically included |
| Our operational effort | Low | Very High | Low |
What we’ve observed is that Fullerton businesses find the most success when they prioritize clarity over brand names. We need to know, without a doubt, who is tweaking the rules, who picks up the phone at night, and how an incident gets resolved.
What Steps Should Businesses Follow to Choose The Right Provider?
A structured process prevents costly mistakes. Teams that just pick a name from a list often regret it. One of the most important steps is defining who actually owns the day-to-day work, including rule updates, monitoring, and escalation. Clear success depends on strong processes for configuring WAF policies and rules so protections stay accurate as applications change.
We’ve seen proper tuning cut false positives by 40% or more, which means a better experience for our customers and less noise for our IT team.
A practical selection process looks like this:
- Map what we have. List our critical applications, APIs, and normal traffic patterns.
- Scope the deployment. Decide if we need a cloud, on-premise, or hybrid setup for our Fullerton operations.
- Test with real traffic. Insist on a proof-of-concept using our actual website traffic, not a demo.
- Read the fine print. Scrutinize the SLA for uptime, response times, and escalation paths.
- Define “ownership.” Confirm exactly who handles tuning, monitoring, and incident response.
We guide our MSSP partners through this process side-by-side. The goal is to find the best fit, not to sell the biggest package. That mindset helps avoid two big traps: overpaying for unneeded features, and under-protecting our most critical assets.
FAQ
How does managed WAF Fullerton support reduce daily security workload?
Managed WAF Fullerton support reduces the daily workload by handling alerts, updates, and rule tuning for you. Instead of letting issues build up, the provider reviews traffic patterns and keeps protections current.
This approach strengthens web application firewall Fullerton defenses over time. It also improves false positive reduction WAF efforts, so real attacks are easier to spot. Many Fullerton cybersecurity MSP services include this ongoing operational support.
What should I ask about OWASP ruleset tuning before signing a contract?
You should ask how the provider manages OWASP ruleset tuning after the system goes live. Poor tuning can cause blocked customers or missed threats. A reliable team explains how they adjust custom WAF rules, improve SQL injection blocking, and maintain strong XSS protection Fullerton sites need. Regular tuning helps ensure consistent Layer 7 protection Fullerton organizations depend on.
Do providers offer DDoS WAF integration with traffic scrubbing Fullerton services?
Many providers offer DDoS WAF integration, but you must confirm what attacks they actually stop. Some services only filter application traffic and cannot handle large floods. Ask whether traffic scrubbing Fullerton support is included, along with HTTP flood blocking and Slowloris prevention Fullerton controls. Strong Layer 7 protection Fullerton plans also include bot mitigation WAF and rate limiting WAF features.
How can PCI DSS WAF compliance and SOC 2 MSP Fullerton overlap?
PCI DSS WAF compliance protects payment systems, while SOC 2 MSP Fullerton standards focus on security controls across the business. Managed security services Fullerton providers often support both by offering 24/7 WAF monitoring, detailed logging, and incident response Fullerton readiness. We should also ask how they document rule changes and maintain audit evidence. Clear processes make compliance easier to achieve and maintain.
What makes a strong WAF SLA in a waf provider California agreement?
A strong waf provider California SLA defines uptime guarantees WAF, response times, and support availability in specific terms. We should ask how they measure threat detection accuracy, apply waf vulnerability patches, and respond to serious incidents. The agreement should also explain escalation steps, local WAF tuning procedures, and what support looks like during major attack events.
Choosing the Right Managed WAF Provider in Fullerton
Choosing a managed WAF provider in Fullerton comes down to trust, operational depth, and consistency. While technology evolves fast, disciplined management and clear accountability stay essential. With the right managed security services, organizations can reduce risk without adding internal burden.
At MSSP Security, we provide vendor-neutral consulting for MSSPs, helping streamline operations, reduce tool sprawl, and improve service quality through auditing, PoC support, and stack optimization. With 15+ years and 48K+ projects, we deliver clear recommendations. Schedule our next step with our team
References
- https://www.indusface.com/blog/how-waf-helps-with-compliance/
- https://aws.amazon.com/marketplace/solutions/security/managed-rules-for-aws-waf/
