Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Automating security playbook execution is one of the most reliable ways MSSPs can protect cloud environments at scale. When an alert hits, a well‑built playbook can investigate, enrich, and contain the threat before anyone in the SOC even moves a…

Your security team is drowning in alerts. We see it all the time. A SOAR platform is the answer. It’s software that connects your security tools, automates the routine tasks, and standardizes your response to incidents. This isn’t just a…

Threat hunting improves security by catching threats that hide quietly instead of waiting for alerts that may never fire. Many teams are finally shifting to this approach because attackers often sit in networks for months, staying just below the noise.…

Expert threat hunter services matter because attackers don’t wait for alerts or line up neatly with your rules. Many slip in quietly, sit still for months, then move across systems in slow, careful steps. Some attacks stay hidden for half…

Proactive security monitoring techniques is what teams use when alerts stop being useful.Most attacks now slip through side doors, hiding in quiet logs and low-priority events that no one has time to study. Many readers know this already, too many…

Threat hunting platform management only works when someone takes control of the platform, not the other way around. Many SOC teams sit under noisy alerts, confusing views, and tools that promise precision but rarely help on a busy day. At…
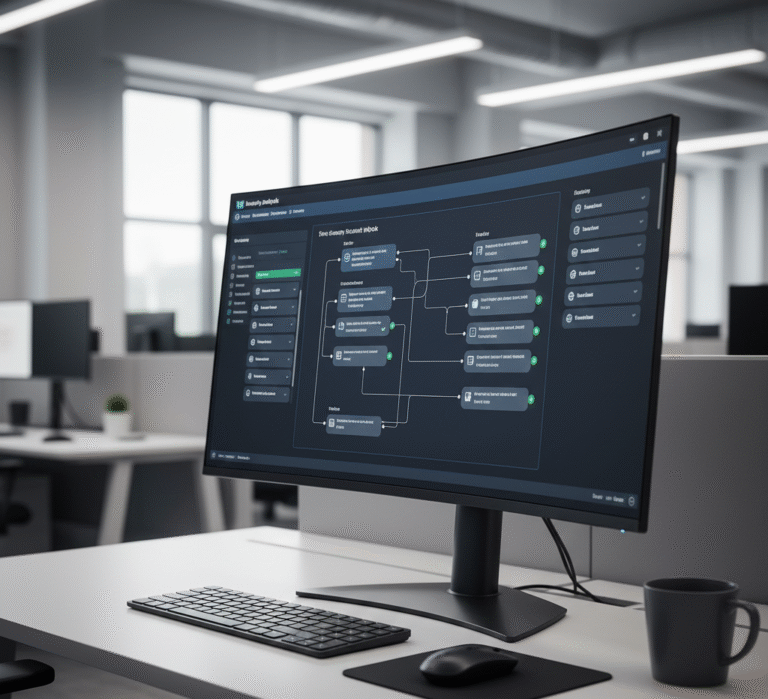
![Visual representation of outsourced cybersecurity threat hunting [city], showcasing threat detection and analytics.](https://msspsecurity.com/wp-content/uploads/2025/11/image-71-768x432.jpeg)
Outsourced cybersecurity threat hunting in Fullerton, California helps teams that already know they’re stretched and don’t want to gamble with blind spots. Attackers move faster than most in-house teams can track, jumping between systems, hiding in normal traffic, waiting. Studies…

APTs move in ways that feel almost quiet, like someone brushing past a doorway you didn’t notice at first. You see their trail in tiny marks, logins that drift past midnight, a file growing by only a few kilobytes, a…

Threat hunting works by using a person’s steady eye alongside tools that pull out quiet signals from wide logs and short bursts of network traffic, and we keep noticing how a small shift in timing can change the whole search. …

What is MSSP threat hunting? Security teams spend too much time waiting. Most sit around watching dashboards for alerts that might never come, but threats don’t always announce themselves. Managed security providers flip this around, they actively hunt through your…