Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

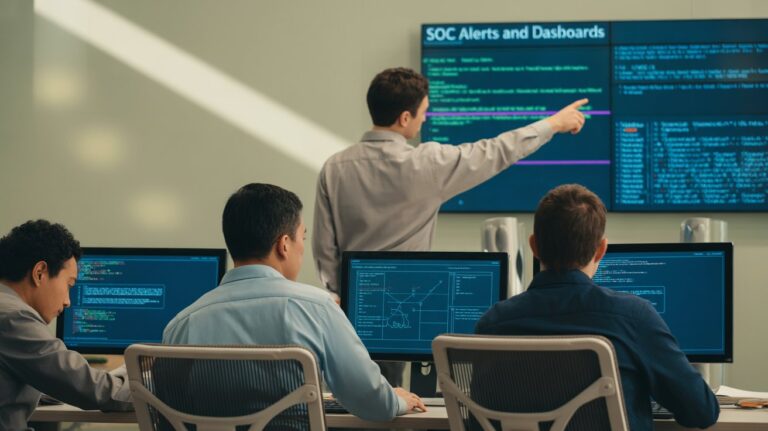
What does a SOC do? A Security Operations Center (SOC) watches over an organization’s systems…

Understanding the SOC function means knowing how cyber threats are found, stopped, and studied. From…
Watching how companies set up their security teams, you start to see patterns, some build…

Most folks probably see it by now, just waiting around for trouble isn’t enough anymore.…