Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Any device connected to a network might be the next target. The mere thought probably…

Endpoint Detection and Response (EDR) management is designed to stop modern threats at the device…

There’s something fascinating about how a simple document transforms chaos into order. Behind the dry…
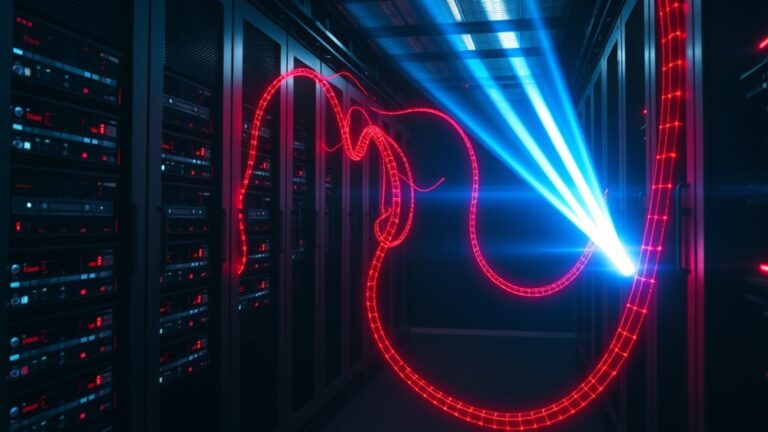
When cyber attackers settle into a network unnoticed, the damage piles up fast. Our experience…