Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

You simulating real world attacks safely to find security gaps before real attackers do. Think of it like a fire drill versus a real fire; it’s the only reliable way to know if your team and tools will hold up.…

Your last penetration test report likely won’t pass an audit. Most standards, like PCI DSS or HIPAA, require documented proof that your key security controls can stop a real attack, not just a list of vulnerabilities. Many technically sound tests…

Forget vendors that just sell you a pass-fail report. You need choosing penetration testing vendor in Fullerton who thinks like an attacker, finds the cracks in your defenses, and sticks around to help seal them up. Demand specifics on their…
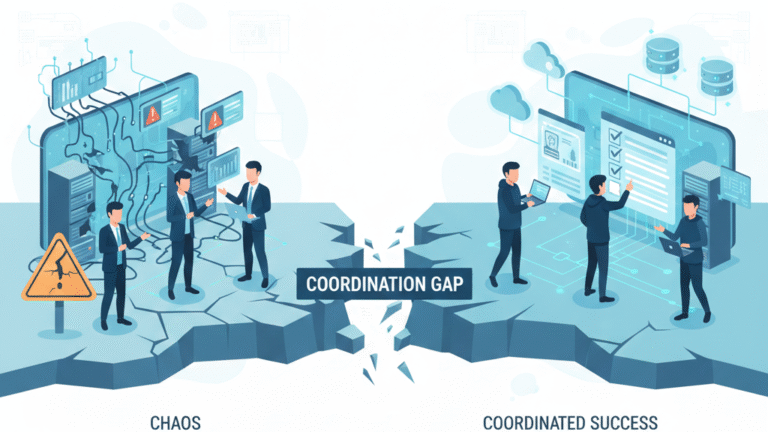
Coordination transforms a chaotic cyber fight into a useful training exercise. It’s the shift from random attacks to a planned session where everyone learns. By coordinating red team blue team exercises together, you build a common understanding across your security…
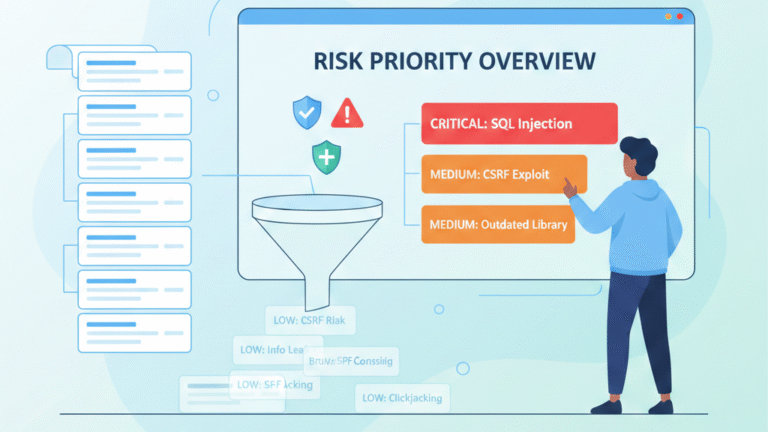
Start with the critical flaws in systems that face the internet, especially if exploit code exists. Next, weigh the business context. A medium bug in a payment portal is usually a bigger problem than a high-severity one on an isolated…
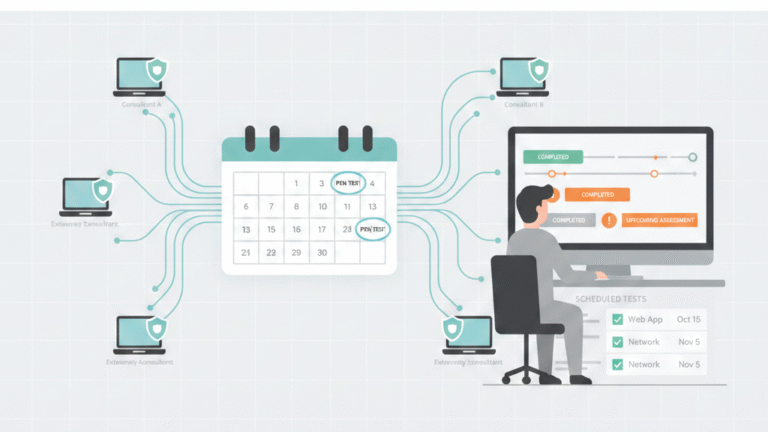
You need a centralized, hybrid model for outsourced pen test scheduling management. This blends automated, continuous scanning with scheduled, manual tests from external experts. It aligns with compliance cycles like PCI DSS, keeping you audit-ready without quarterly production halts. Ditch…

You have the report. The real security work starts now. Managed pen test coordination, often handled by a Managed Security Service Provider (MSSP), makes sure those critical findings get fixed. It turns a one-time security snapshot into an ongoing process…
Getting a penetration testing coordination approved is just the first step. If you simply hand over the keys and wait, you risk an outage or a useless report. The real work happens before the hackers start. Success depends entirely on…

The Purdue Model security monitoring is a practical blueprint for industrial security. It segments your operational technology into clear zones, creating defensible layers. This gives you the visibility to spot problems before they escalate. Forget the abstract theory. This guide…
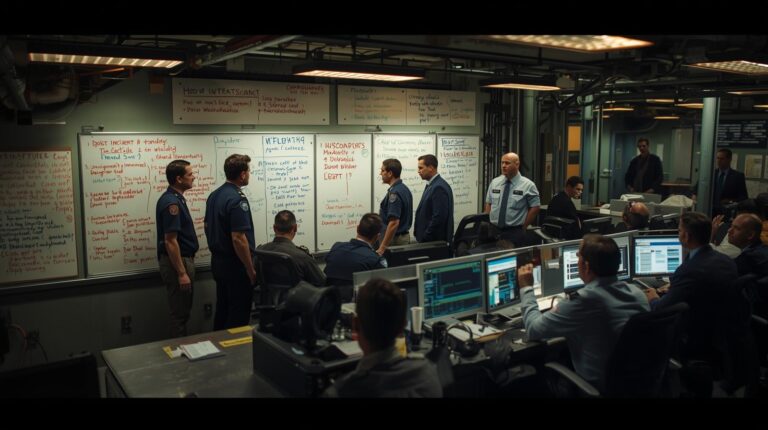
ICS incident response planning is the use of the Incident Command System to manage cyber and operational incidents in industrial control environments such as SCADA, PLCs, and critical infrastructure. In our work supporting utilities and manufacturers, we see that standard…