Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
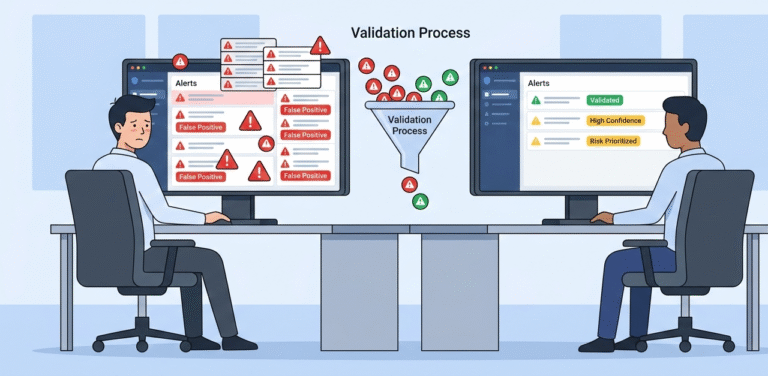
Using threat intelligence triage cuts through alert noise. It uses external data, like known malware or attacker methods, to quickly validate alarms. Good programs see false positives drop by 30%. This turns a flood of data into a short list…
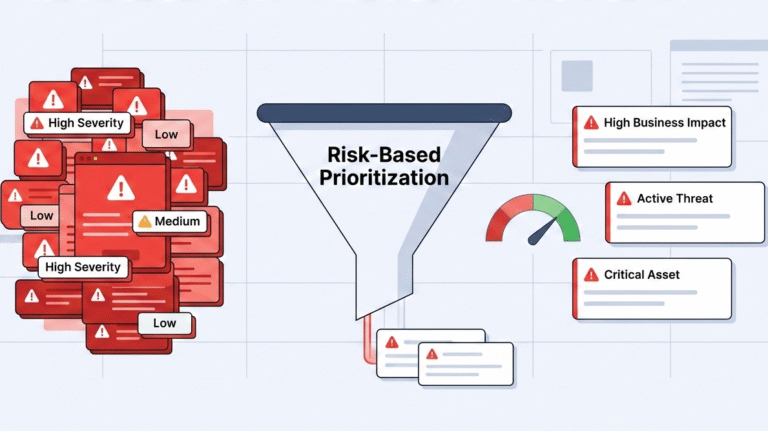
You’re staring at a dashboard blinking with a thousand identical red warnings. Which one is the real fire? Traditional alerting doesn’t know. It treats a vulnerability on a public database the same as one on a developer’s test machine. The…
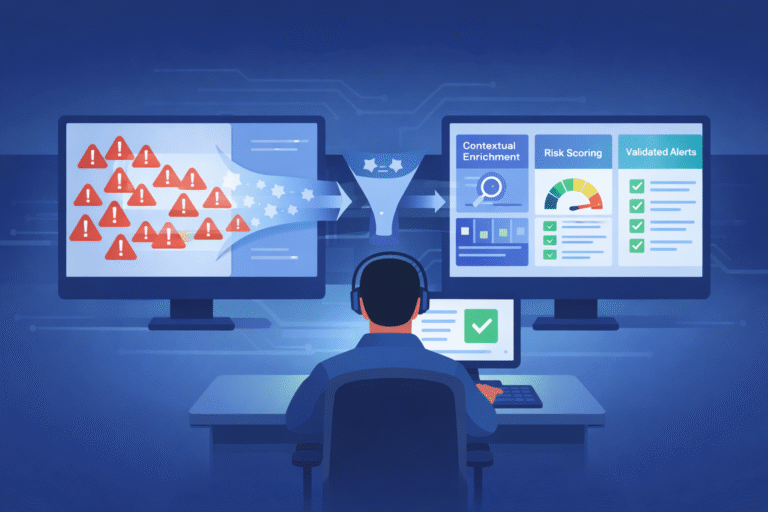
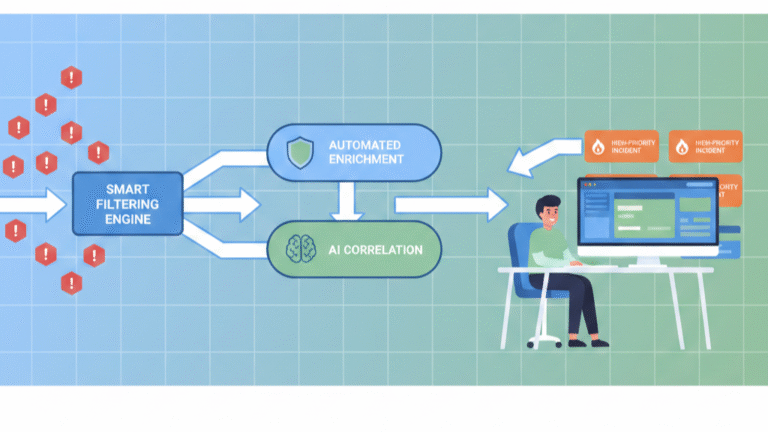
The noise is drowning out the signal. You’re not just getting security alerts; you’re getting buried by them. Alert validation is the systematic process of verifying which of those pings are genuine threats and which are just digital ghosts. It’s…
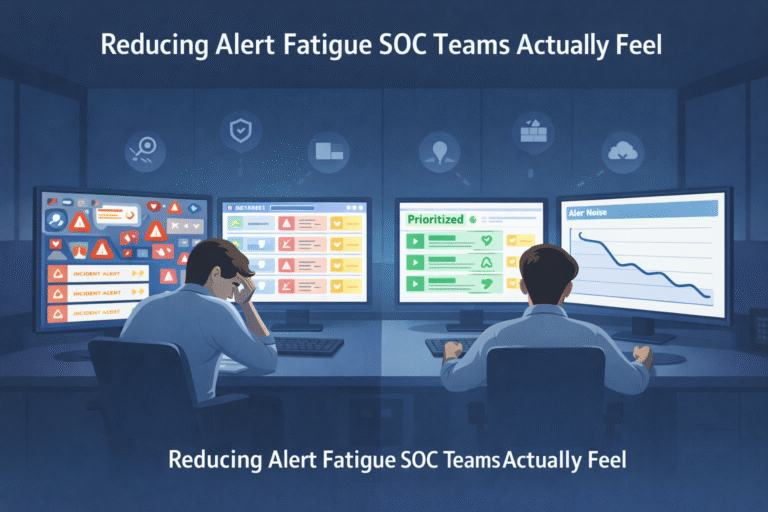
Alert fatigue is the slow, grinding burnout that happens when your security team drowns in a sea of meaningless notifications. It’s not just about volume, it’s about value. When analysts face thousands of alerts daily, with a staggering 99% being…
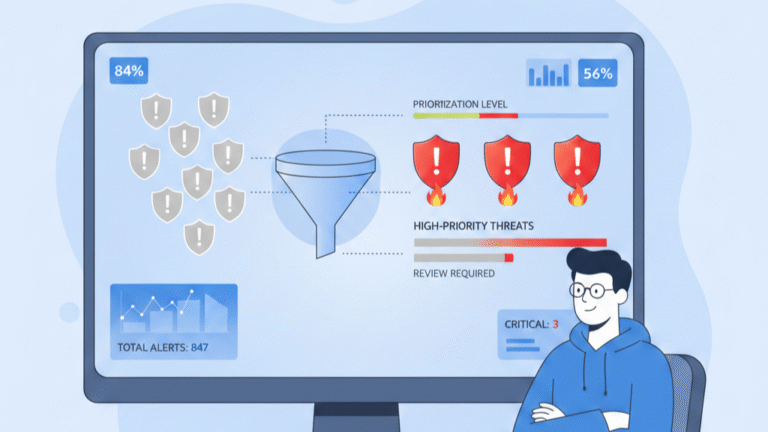
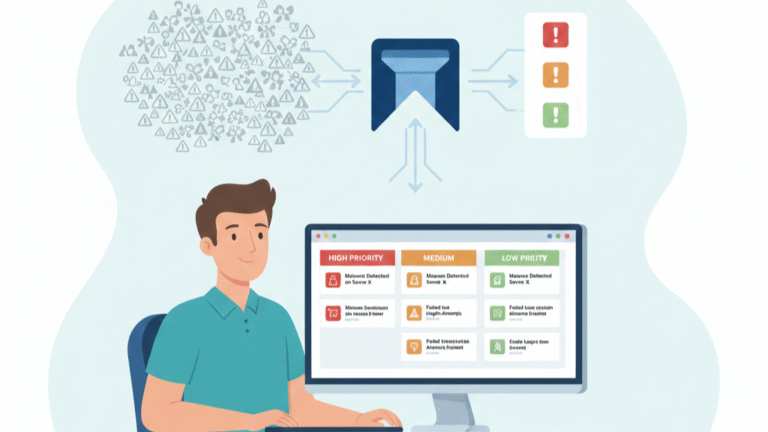
You can’t fight every fire at once. How security alerts are prioritized is the triage system that stops your team from drowning in noise and focuses them on the real breaches. It’s the difference between chasing false positives and neutralizing…
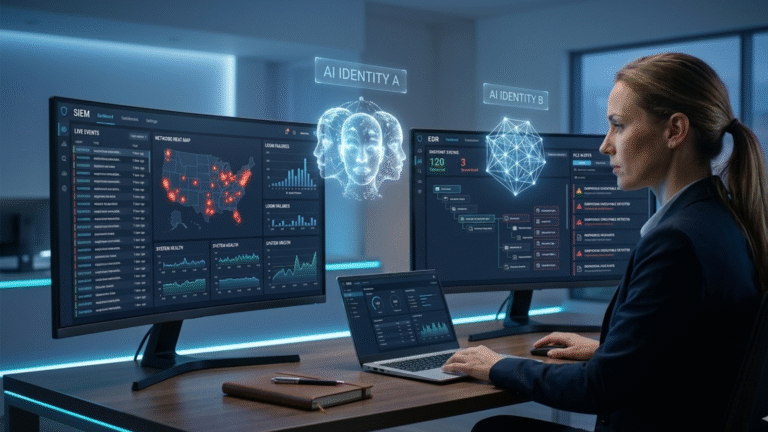
By MSSP Security Consulting Research Team Look, we spend our days inside MSSP stacks. We audit them, we optimize them, and lately, we’ve been noticing something disturbing. The tools everyone relies on to detect threats? They’re blind to half the…
We watched an analyst waste forty minutes on a false alarm yesterday. He jumped between six screens for a “high severity” ransomware alert. It was just a clumsy admin tool. While he worked, three more alarms piled up. This is…
A good MSSP alert handling process cuts through the noise. It uses a standard workflow to separate real threats from false alarms, so your team isn’t swamped by thousands of meaningless alerts. The real work happens after you invert that…
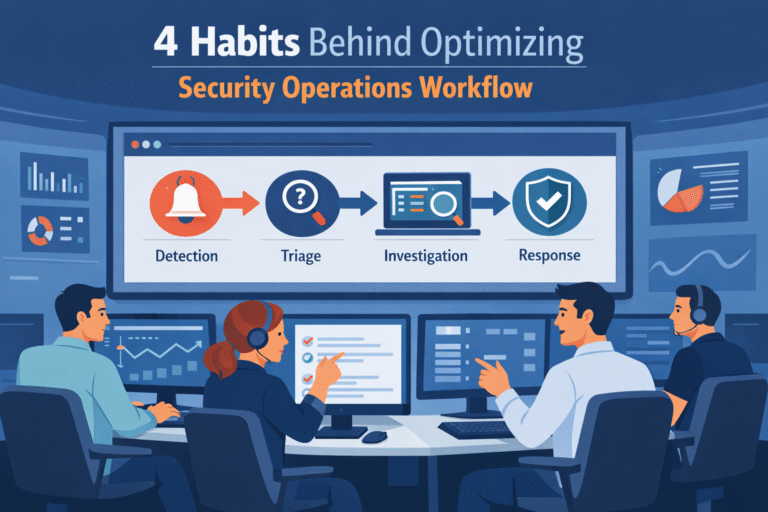
Optimizing security operations workflow starts with fixing the process, not blaming the analysts. When the workflow is unclear, teams lose time deciding what to check first. A clear path for each alert changes that. It tells analysts what comes next…
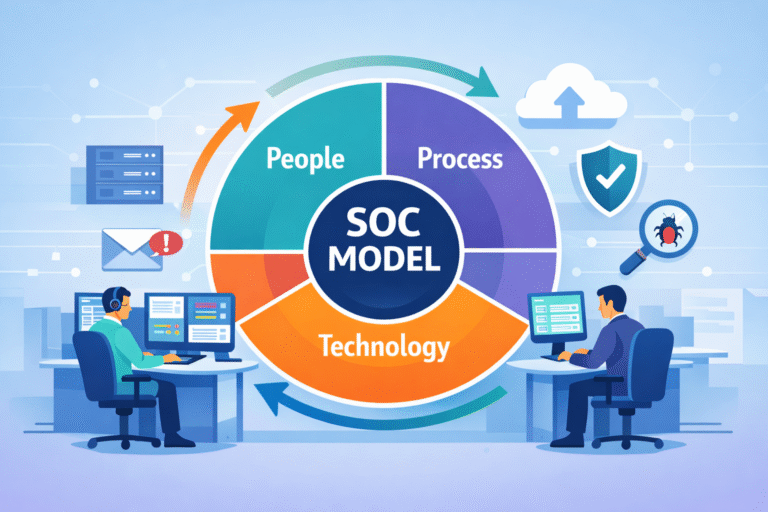
Understanding SOC operations model starts with one idea: structure decides outcomes. A SOC model defines how people, process, and technology work together against threats. Cybercrime keeps rising, but tools alone don’t solve it. We’ve seen environments packed with modern platforms…