You’re buying more security software, but feeling less secure. The problem isn’t a lack of tools, it’s a critical surplus. The real solution is a vendor-agnostic audit of what you already own. This process, a stack audit, cuts through the noise, reveals hidden costs, and turns your bloated tech stack from a liability into a streamlined defense. Keep reading to learn how the data proves that less, when properly audited, is definitively more.
Key Statistics on The “80 Tools” Crisis
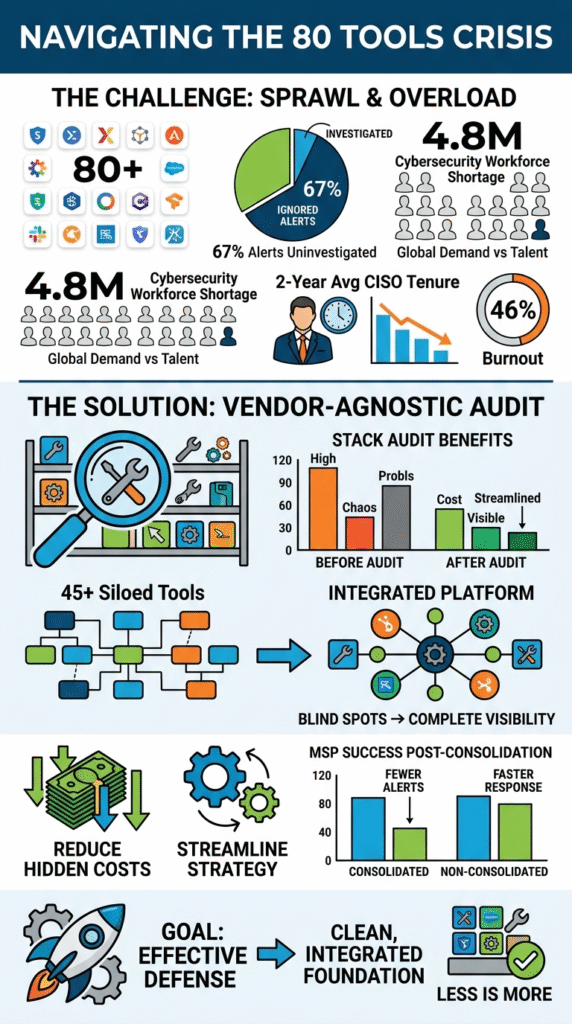
The scale of the tool sprawl problem is no longer anecdotal, it’s quantifiable. Recent industry surveys and analyses paint a stark picture of integration failure, alert overload, and the severe operational and financial consequences. Here are the ten statistics that define the modern security tool crisis.
- 89% of MSPs struggle with tool integration; 56% experience alert fatigue daily or weekly – This highlights the near-universal failure to create cohesive security ecosystems, leading to daily operational strain.
- 67% of security alerts go uninvestigated; average enterprise SOC ingests 1,000-10,000 alerts per day – This shows a structural breakdown where the volume of data far exceeds human capacity to process it, making most alerts useless.
- 70% of CISOs are consolidating security tools into integrated platforms; 68% rely on MSSPs – A clear majority of security leaders recognize consolidation as a strategic imperative, often outsourcing the complexity.
- Global cybersecurity workforce shortage: 4.8 million professionals; must grow 87% to meet demand (grew only 0.1% last year) – The talent pipeline is broken, forcing organizations to do more with fewer people, making tool efficiency non-negotiable.
- 75+ security tools managed by average enterprise; ~2,000 security alerts per week – This quantifies the sheer scale of tool sprawl and its direct output: an overwhelming, unmanageable alert factory.
- Average enterprise runs 45 different security tools that “work in silos, creating complexity, blind spots and unidentified exposures” – Gartner identifies the core issue: it’s not just the number of tools, but their isolation that creates dangerous gaps in coverage.
- Average CISO tenure: just 2 years (vs. 5 years for other C-suite roles); 46% of security professionals exit roles primarily due to burnout – Tool sprawl and alert fatigue have a human cost, driving experienced leaders out of the industry at an alarming rate.
- Only 11% of MSPs report seamless tool integration; 20% juggle 7-10 tools; 12% manage 10+ – For service providers, seamless operation is a rare exception, not the rule, with most managing a chaotic array of point solutions.
- Only 20% of MSPs have consolidated their security solutions; those who did report fewer alerts, faster response, and happier staff – This is the proof of concept: a small minority who have acted report dramatically better outcomes across the board.
- Global MSSP market to reach $506.48 billion by 2035 (CAGR 8.5% from 2026) – The market is voting with its wallet, signaling massive, sustained growth for outsourced security management as internal tool sprawl becomes untenable.
Here are the sections revised and expanded with the specific citations and data points provided:
89% of MSPs Struggle with Tool Integration
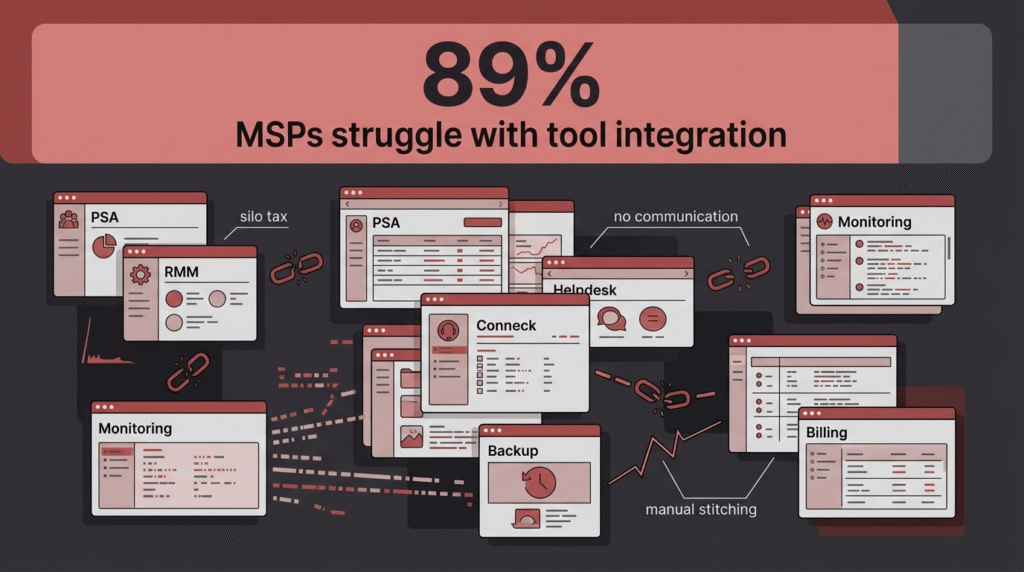
That number feels almost too high to be real, doesn’t it? Yet, according to the Heimdal & FutureSafe “State of MSP Agent Fatigue 2025” survey, nearly nine out of ten managed service providers cannot make their security tools work together properly. This isn’t a minor inconvenience; it is the “silo tax” in action.
Each tool operates in its own isolated environment, generating data that doesn’t communicate with the platform sitting right next to it. Analysts are forced to become human integration platforms, mentally stitching together clues from five different consoles.
It creates friction, slows every response to a crawl, and guarantees that the full picture of a threat is almost never seen. The root cause is often a mix of vendor lock-in and a lack of standardized, open APIs. Companies buy what seems best for one problem without a plan for the whole, resulting in:
- Manual correlation of data across consoles
- Inability to automate cross-platform workflows
- Duplicate licensing for overlapping features
- Constant context-switching for analysts
This integration hell means your security posture is only as strong as your most isolated data silo. And with 89% of providers stuck there, it’s a sector-wide vulnerability.
67% of Security Alerts Go Uninvestigated
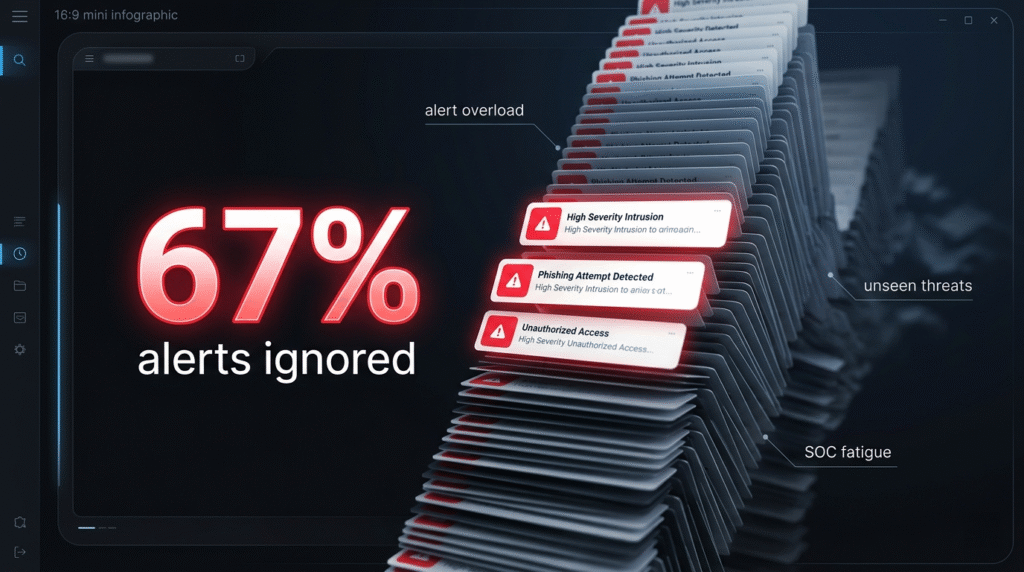
Think about that for a second. Two-thirds of all the alarms your security system raises are simply ignored. They flash on a screen somewhere, maybe get logged, and then disappear into the void. The reason isn’t apathy; it’s simple arithmetic.
Data from a D3 Security analysis of SOC operations (March 2026) reveals that 67% of security alerts go uninvestigated because the average enterprise SOC ingests between 1,000 and 10,000 alerts every single day. An analyst working a standard shift can maybe triage, investigate, and properly document about 21 alerts if they are pushing hard. The math simply doesn’t work. It’s a structural impossibility.
This turns the Security Operations Center into an “alert factory,” a place that manufactures noise at an industrial scale. Buried in that 67% of ignored alerts could be the one that signals a real, ongoing breach. But it’s lost, a single shout in a raging hurricane. Teams are forced to play a brutal game of odds, guessing which alerts might be serious based on crude filters and gut feeling. It’s security by gambling, not by design.
70% of CISOs Are Shifting Toward Security Tool Consolidation
The data shows a clear pivot in strategy. According to the IANS & Artico Search “Security Software and Services 2025 Benchmark Report,” 70% of CISOs are now actively moving away from collecting point solutions. The era of buying a new widget for every new threat is ending. Instead, the focus is on integrated platforms, suites that promise to handle multiple functions from a single pane of glass.
Why the sudden shift? The pain of managing 45 siloed tools has finally exceeded the perceived benefit of “best-of-breed” for every single category. CISOs are tired of the integration, budget, and staffing fights that tool sprawl creates.
They are choosing sanity. Furthermore, the report notes that 68% of these leaders are leaning on Managed Security Service Providers (MSSPs) to execute this consolidation. It’s an admission that untangling this self-made knot is a specialized job, requiring a vendor-agnostic perspective to objectively evaluate what to keep, what to integrate, and what to cut.
The Global Cybersecurity Workforce Shortage is 4.8 Million Professionals
The gap isn’t just widening; it’s a chasm. The ISC2 Cybersecurity Workforce Study 2025 indicates that the industry needs 4.8 million more skilled professionals than it currently has. To meet demand, the workforce would need to grow by 87% overnight, yet it grew by only one-tenth of one percent (0.1%) last year.
The traditional model of “hiring more analysts” to handle more tools is a fantasy; the people simply do not exist. This shortage changes the security equation, making every tool decision a “force-multiplier” decision. You cannot evaluate software based on features alone; you must evaluate it based on operational efficiency.
How much human time does this tool consume versus how much value does it provide? This brutal math is a primary driver behind the move to consolidated platforms. If you can’t hire the people, you must leverage technology that maximizes the impact of the people you already have.
Managing 75+ Security Tools Actually Decreases Safety
It sounds counterintuitive, more tools should mean more safety. However, March 2026 research from PENTERA screams the opposite. The average enterprise now manages over 75 security tools, which collectively generate roughly 2,000 alerts every week. This massive tool count doesn’t create a net of security; it creates a dense fog of noise.
Complexity itself becomes the vulnerability. Analysts suffer from “tool whiplash,” and real threats slip through the cracks because they were lost in the deluge.
| Tool Sprawl Metric | Enterprise Average | Direct Consequence |
| Total Security Tools | 75+ | High complexity and administrative overhead |
| Weekly Alert Volume | ~2,000 | Severe analyst alert fatigue and burnout |
| Tools Operating in Silos | 45 | Critical visibility gaps and blind spots |
The goal isn’t a magic number of tools; it’s achieving coverage with the minimal, most integrated set possible. Every new tool must justify its existence against the operational burden it adds.
45 Different Siloed Tools Create Critical Blind Spots
Gartner’s December 2025 report, “Tech FutureSight,” highlights that the average enterprise runs 45 different security tools that work in silos. This creates “complexity, blind spots, and unidentified exposures.”
This is the technical reality of the integration crisis. A firewall doesn’t talk to the endpoint detection system, which doesn’t share data with the cloud security manager. An attacker, however, moves freely across these boundaries.
Your tools see fragments of the attack, isolated pixels, but no single system can assemble the full picture. The blind spot isn’t a lack of a tool; it’s the gap between tools. Realizing you have 45 siloed tools is the scary part, 10 well-integrated tools provide far more usable security than 45 disconnected ones.
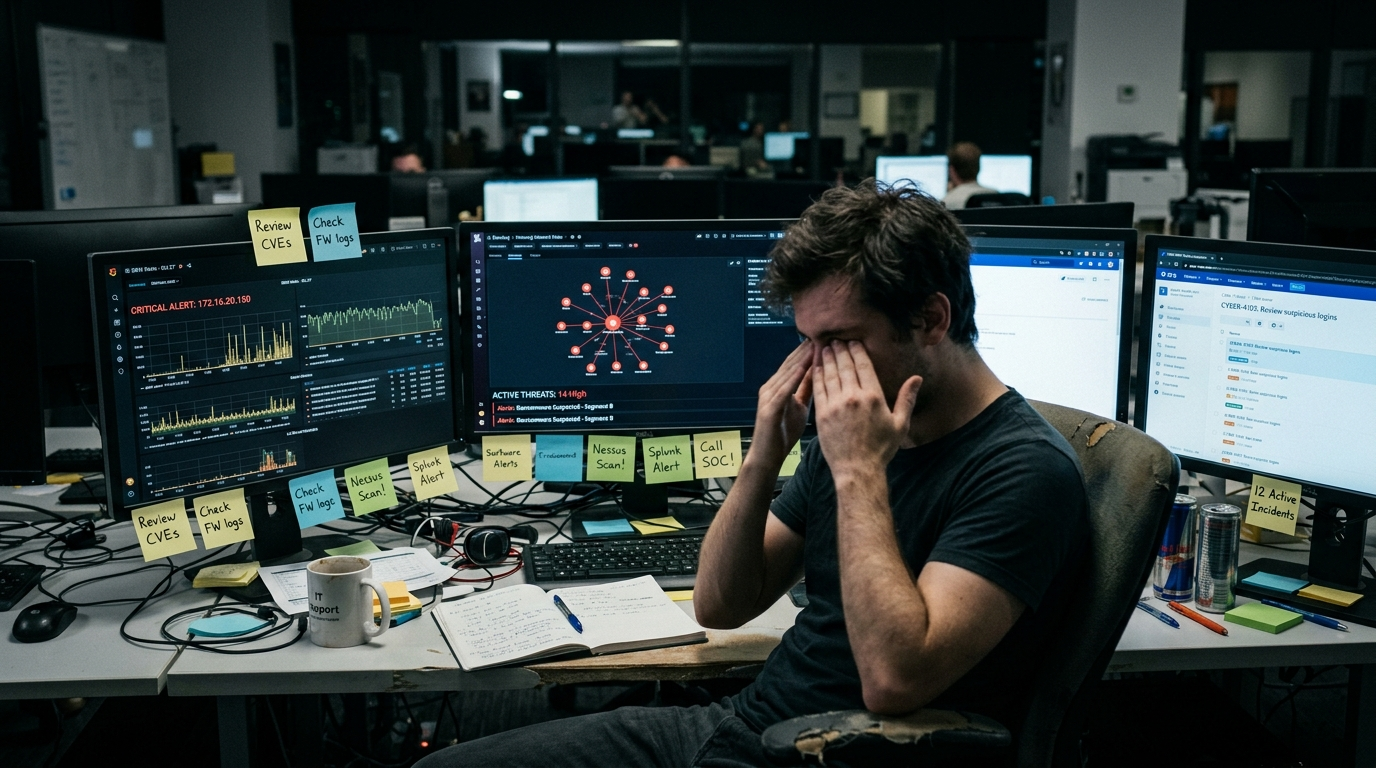
The 2-Year Average CISO Tenure is a Direct Result of Burnout
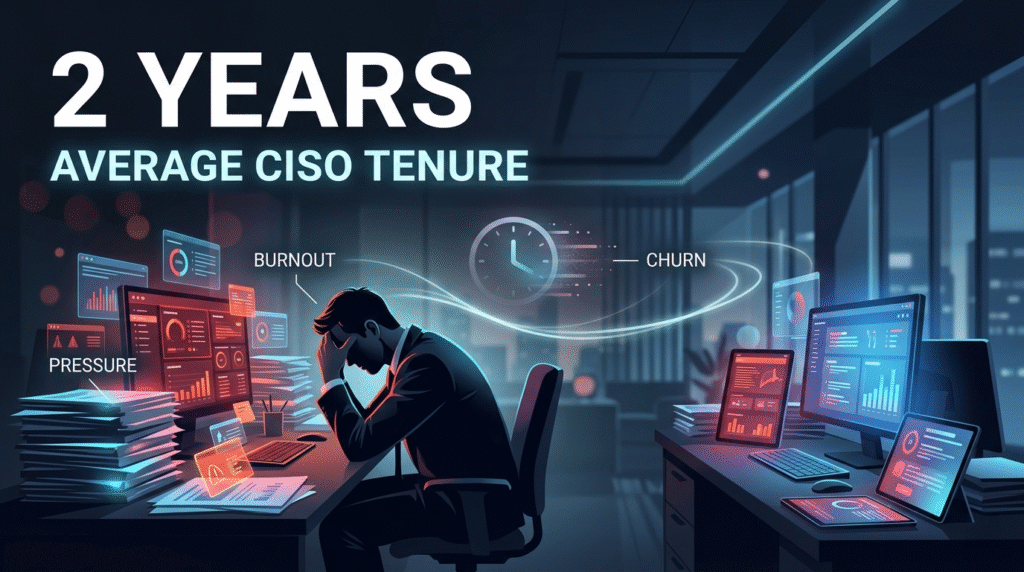
Two years, that’s all the average CISO lasts in their role, compared to the five-year tenure common in other C-suite positions. According to LinkedIn data from March 2026, this staggering churn is driven by exhaustion, with 46% of departing security professionals citing burnout as the primary reason.
These leaders are fighting a war on two fronts: external threats and internal tool chaos. They are held accountable for breaches that slip through fragmented, noisy systems they often inherited. Managing alert fatigue, staffing shortages, and the 67% of unchecked alerts creates an unmanageable weight.
Fixing the security stack is no longer just about efficiency; it is essential for the long-term sustainability of the people leading the defense.
Only 11% of MSPs Achieve Seamless Tool Integration
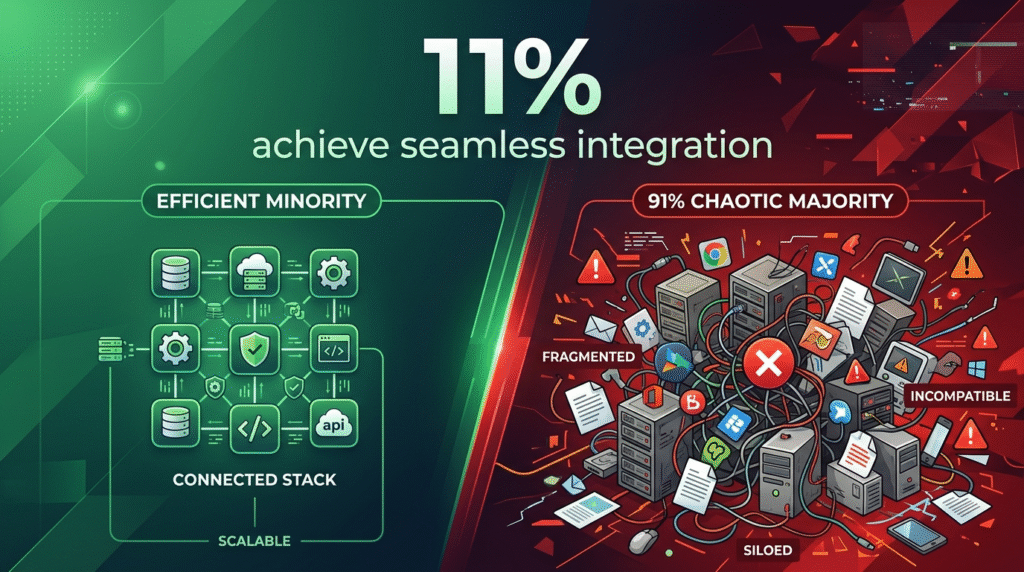
According to the Heimdal & FutureSafe 2025 survey, if tool integration were a test, 89% of MSPs would be failing. Only 11% of MSPs report achieving seamless integration. The rest are caught in the grind: 20% juggle 7 to 10 different tools manually, while 12% manage more than 10.
This isn’t a scalable business model; it’s a tech support nightmare. The inability to integrate forces MSPs to throw expensive analysts at low-level tasks, killing profit margins.
For an MSP, a rationalized, integrated stack is the core of operational leverage. The 11% who have cracked this code aren’t just more secure; they are running significantly more profitable businesses.
The 20% of MSPs That Consolidated Reaped Major Benefits
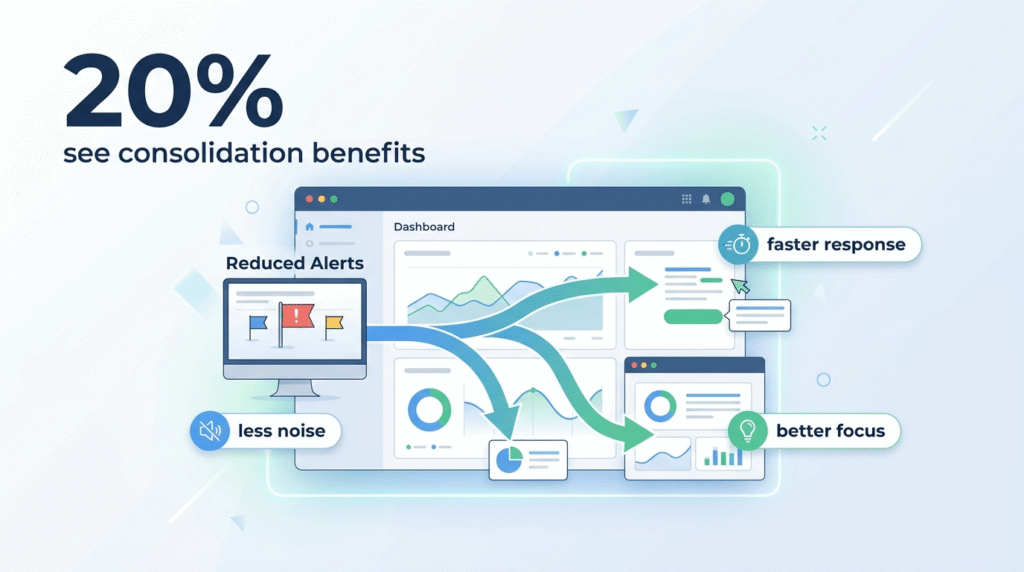
The Heimdal & FutureSafe survey also found that a small group, only 20% of MSPs, have fully consolidated their security solutions. This minority serves as a proof of concept for the rest of the industry.
These MSPs report fewer alerts, but more importantly, they report the right alerts. By dropping the noise floor, real signals are finally heard. This leads directly to faster response times and happier staff. Reduced context-switching and less manual busywork combat burnout. Their experience provides a clear blueprint: audit ruthlessly, integrate aggressively, and manage what’s left, not what’s accumulated.
The MSSP Market Will Reach $506.48 Billion by 2035

According to Business Research Insights (February 2026), the global MSSP market is projected to reach $506.48 billion by 2035, growing at an annual rate of 8.5%. This isn’t just a financial forecast; it’s a market verdict. The world is betting that most organizations cannot solve the tool sprawl crisis internally.
Internal teams are hitting a ceiling where adding more tools creates diminishing returns. Businesses are now voting with their budgets, handing off the “tangled knot” of tools and alerts to specialists. MSSPs that can deliver a rationalized, integrated service are positioned to capture this demand.
The future of security isn’t an in-house arsenal of point solutions; it’s a curated, managed service built on a clean, audited, and fully integrated foundation.
Navigating the 80 Tools Crisis
The data leads to an inescapable conclusion. The path to greater security and lower cost does not start with a purchase order for another tool. It starts with a pause, and a hard look inward. A vendor-agnostic stack audit is the flashlight for that look.
It moves you from guessing to knowing. You’ll see the redundant licenses, the overlapping tools, the silent integrations that broke six months ago, and the critical gaps between your silos. This audit isn’t an IT exercise, it’s a strategic one. It directly addresses the burnout, the wasted budget, the missed alerts, and the blind spots.
The goal is not necessarily to have fewer tools, but to have the right tools, working in concert. In a world of 4.8 million missing professionals and 67% ignored alerts, efficiency isn’t just a goal, it’s the only viable defense. Start with an audit. Understand what you truly have, and only then can you build what you actually need.