Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
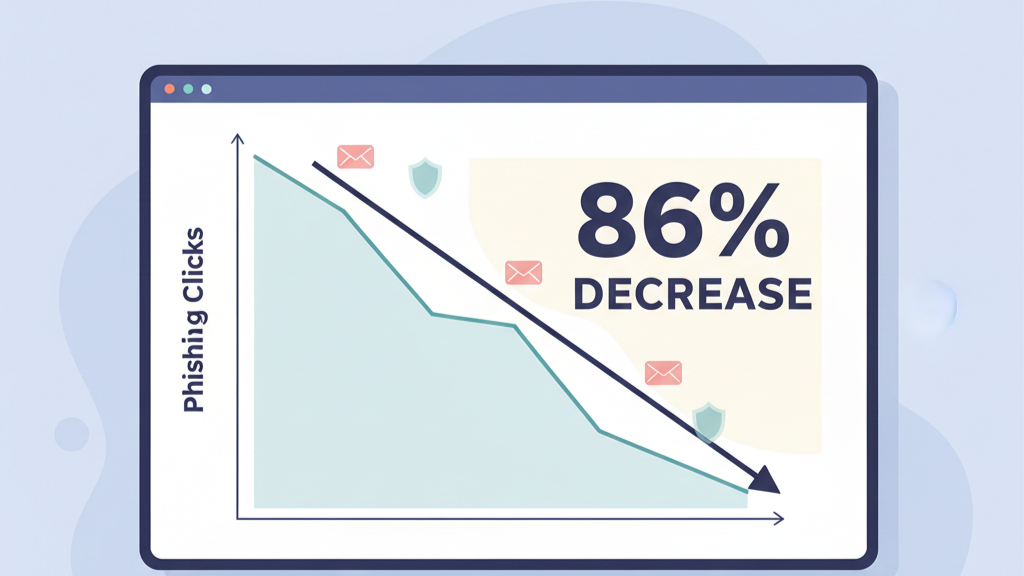
Yes, training works. Consider this: in one year, consistent security awareness training management reduced the average phishing click rate from 33% to just 4%, based on data from over 67 million simulations. That’s an 86% improvement.
The goal isn’t to tick a box. It’s to make security a reflex for your team, transforming them from a risk into your first line of defense. The hard part is making that change stick. Find out how to build a program that does. Keep reading to transform your human risk from a liability into an asset.

A company can spend a fortune on the latest firewalls and detection software. Then one person clicks a link, and the whole defense is compromised. It happens constantly. Studies show human error is a direct cause in 60% to 74% of all breaches.
“In every organization I’ve worked with, the biggest difference between average security and great security comes down to how people think, not what tools they use. Technology can stop malware, but only culture can stop complacency.” – VEEAM
A managed security awareness program directly tackles this problem. It turns security education from a yearly HR task into an active, measurable part of your security operations.
Running this program internally is a huge job, especially for teams without a full-time security leader. Someone has to find and update the training content, schedule it, run realistic phishing simulations, and track the results. This is exactly where our partnership with MSSPs comes in.
We take on that operational burden, the campaign management, the reporting, the compliance tracking, so your team doesn’t have to. From our experience, the result is a living program that adapts as threats change, not a static annual requirement you just check off.
Credits: OutThink
Outsourcing your phishing simulation training offers two major benefits: you gain scale and deep expertise. Creating believable, multi-stage simulations that copy modern AI-driven attacks is a specialized job. A good provider will have a massive, constantly updated library of templates for everything from vishing calls to AI-generated emails.
The results speak for themselves. Companies that run these continuous tests often see phishing click rates fall by 40% in the first three months. Even better, the rate at which employees report suspicious messages goes up. Regular, safe testing teaches people to flag potential threats, creating a vital early-warning system for your whole organization.
By handing this to a specialist, like an MSSP, you ensure the simulations are sophisticated, the feedback is immediate, and the reporting is clear. It delivers a high-impact security control without draining your own IT team’s time and energy.
If you can’t measure it, you can’t manage it. Measuring security awareness effectiveness requires moving beyond completion rates. True metrics focus on behavior change and risk reduction.
These metrics, visible on a unified Security Awareness Report dashboard, translate training activity into tangible security posture improvement. They provide the proof points for leadership on ROI, showing how training directly reduces cyber risk and potential breach costs.
Selecting a security awareness training platform is pivotal. The wrong choice leads to disengaged users and stagnant metrics. Look for platforms that do more than host videos.
| Critical Feature | Why It Matters |
| Adaptive, Role-Based Learning | Content adjusts to the learner’s job function and past performance, making it relevant. |
| Multi-Channel Simulation Library | Must include email, SMS, voice, and QR code phishing to match the modern threat landscape. |
| Integrated Metrics & Reporting | Provides clear dashboards on PPP, reporting rates, and risk scores for easy measuring security awareness effectiveness. |
| Automated Compliance Reporting | Generates auditable logs for regulatory frameworks like PCI DSS, saving administrative time. |
| Seamless Integrations | Connects with your HR system (e.g., Active Directory) for automated user management. |
The platform should feel like a partner in building your security culture, not just a content repository. In our practice, we vet platforms against these criteria to ensure they deliver sustained engagement, not just a one-time launch.
Customizing training content roles is the antidote to generic, forgettable training. A finance team needs deep-dive modules on Business Email Compromise (BEC) and invoice fraud. Your developers need training on securing code repositories and managing API keys. Executives require focused briefings on deepfake impersonation and vishing scams.
“Behavior change should be the primary goal of your security awareness training program. You want users to break bad habits and learn new skills (and how to apply them) in general. But you also want to address risky behaviors that are most likely to impact your organization’s mission.” – Spambrella
This approach respects the employee’s intelligence and daily reality. When training mirrors the specific social engineering attacks they might face, engagement and retention soar.
Studies show role-based training can improve performance among high-risk users by over 45% in six months. It moves the needle because it’s practical. It answers the question, “What does this mean for me and my job today?”
For many organizations, compliance requirements security training is the initial driver. Regulations like GDPR, HIPAA, and PCI DSS mandate regular security awareness education. The requirement isn’t just to “provide training,” but to document it, proof of completion, assessment scores, and program scope.
A robust platform automates this evidence-gathering. It can show that 92% of employees completed their quarterly module with an 85% average quiz score, for instance. This turns a compliance obligation into a structured advantage.
By building your program to meet these regulatory frameworks, you ensure a baseline of ongoing security education reinforcement is met, which simultaneously addresses core human risk. The key is to view compliance as the floor, not the ceiling, of your program’s ambition.

The core mission is reducing human error risk security. Training aims to build new mental habits. It’s not about memorizing a list of threats; it’s about fostering a reflex to verify. A well-crafted simulation doesn’t just test if someone clicks a link. It trains them to hover over the sender’s address, to question urgent financial requests, and to use a reporting button.
This habitual vigilance is what cuts errors. Data indicates companies with active programs reduce employee-driven security incidents by up to 72%. The training transforms the employee from the weakest link into a skeptical, observant node in your defense network.
Each reported phish is a potential incident stopped, making reducing human error the highest-ROI activity in your security budget.
Training shouldn’t live in a silo. Integrating training incident response creates a powerful feedback loop. When a real phishing attack is reported, that event becomes a priceless training moment.
A quick, contextual micro-lesson can be sent to the entire company or specific departments: “Here’s what this real threat looked like, and here’s why reporting it helped us.”
Conversely, your incident response playbook should include steps informed by training data. Knowing which departments have higher risk scores can guide investigation priorities.
This integration ensures your security awareness training programs are informed by real-world threats, and your IR team is bolstered by an aware workforce. It closes the circle between preparation and action.
Building security culture organization is the ultimate goal. Culture is what happens when the CISO isn’t in the room. It’s the salesperson double-checking a wire transfer request, or the HR coordinator questioning an irregular data export. Culture is built through consistent, visible action.
This cultural shift is what sustains gains. It moves security from a set of rules to a shared value, embedding a security-first culture into your organization’s DNA.

Knowledge decays without reinforcement. The Ebbinghaus Forgetting Curve shows we forget about 70% of new information within 24 hours without review. This is why ongoing security education reinforcement is non-negotiable. An annual training session is practically useless.
The modern approach is micro-learning: bite-sized, 3–5 minute lessons delivered monthly or quarterly. This could be a short video on a new ransomware tactic or a quiz on MFA best practices. These monthly touchpoints keep security top-of-mind, gradually building and retaining knowledge.
It’s the steady drip that wears away at complacency and forges resilient habits. This continuous cycle of education, simulation, and feedback is what transforms a program from a cost center into a strategic defense layer.
A strong security awareness program teaches employees how attackers think and act. Through clear training content, real phishing simulation exercises, and regular monthly touchpoints, people learn to spot suspicious activity early.
This lowers user risk, limits costly security incidents, and strengthens overall security posture. Over time, awareness becomes habit, turning everyday staff into a frontline defense against cyber risk.
Many phishing scams now use AI-powered social engineering attacks, voice phishing, SMS phishing, and realistic GenAI email phishing. Basic training often becomes outdated and fails to match real tactics.
Without simulated phishing tests and refreshed security awareness content, employees don’t recognize evolving threats. Continuous, realistic practice is what builds lasting phishing awareness and protects sensitive Information Security assets.
One-time sessions fade fast. A comprehensive security awareness program uses ongoing learning, simulated social engineering, personalized phishing awareness training, and frequent reinforcement.
Employees repeatedly practice handling security threats like ransomware attacks and phishing scams. This builds a security-first culture where safe behavior becomes natural, improving long-term security posture instead of short-term compliance results.
Phishing simulation exposes users to realistic phishing templates that mirror actual cyber threats. When someone clicks, targeted coaching explains what went wrong and how to respond better next time.
This hands-on learning quickly reduces repeat mistakes, strengthens phishing defense habits, and lowers human risk. Over time, employees become faster at reporting suspicious activity instead of falling for attacks.
Building a resilient security posture means systematically managing your people as your first line of defense. The evidence is solid: structured, ongoing training significantly reduces risk and builds organizational strength.
This shift requires the right partners, a focus on measurable outcomes, and a culture of shared responsibility. It’s an ongoing effort. For teams stretched thin, an MSSP partnership can deliver the necessary expertise and sustained focus.
To support this, you need a tech stack that works. We help MSSPs select, audit, and optimize the right tools to cut costs and improve visibility. Let’s build yours.