An interpreting penetration test results lists security flaws, how they can be exploited, and how to fix them. It ranks the risks so your team knows what to handle first. The hard part is figuring out what to do with that information.
We’ll break down how to turn those technical results into a straightforward plan for your business. Learn how to move from a list of vulnerabilities to stronger security.
Security Insights You Should Act on Immediately
- Decode the report structure to separate high-level risk from technical detail.
- Prioritize vulnerabilities using a simple formula of severity and business impact.
- Build a collaborative remediation workflow that fixes the root cause, not just the symptom.
The Anatomy of a Penetration Testing Report

You’ve got the report, maybe 50 pages thick. We’ve seen them, dense with summaries and jargon. The first step is to understand its parts. It’s not just a list of flaws, it’s a story about your security at a specific moment.
“The real value is translating these details into business impact. When viewed through that lens, the report becomes more than a checklist, it’s a strategic asset for staying secure… Don’t let the CVSS score call all the shots. Context matters. Internal vs external risk, compliance concerns, and the potential business hit should shape your plan.” – Datcom Blog
The executive summary is for leadership. It answers one question: are we in immediate danger? Then comes the scope, which defines the battlefield. Was it just the public website, or the internal network too? This sets the boundaries.
The findings are the core. Each one tells a story: the vulnerability, how we exploited it, and what we could access. Look for proof like screenshots. A finding without proof is just a theory. Finally, the remediation advice is your to-do list, ranked by CVSS scores from 0 to 10.
- Executive Summary: The “so what” for your board.
- Scope & Methodology: The rules of the engagement.
- Detailed Findings: The evidence of your security weaknesses.
- Risk Ratings & Remediation: The prioritized path forward.
How to Prioritize What to Fix First
Credits: ACI Learning
When you’re staring at a long list of findings, the question is always: what do we fix first? Not all critical items have the same impact. A SQL injection flaw on your customer login page is a disaster. The same flaw on an isolated, internal test server? That’s a different story.
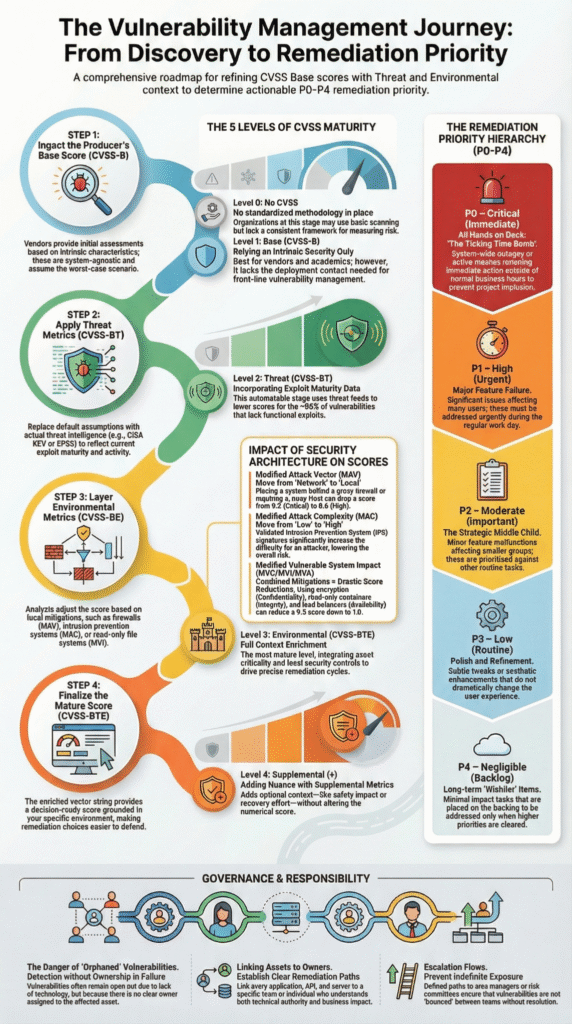
Start with the CVSS score as a technical baseline, anything above a 9.0 needs immediate attention. But then you have to add context. Is the system public-facing? Does it process payment data or personal information? Real risk is a combination of technical severity and how important the asset is.
A medium-severity issue on your core database often matters more than a critical flaw on a static marketing site.We’ve been in those meetings. One client had a report full of “high” risks, but after we looked, most were on old systems they’d already retired. The table below is a practical way to start sorting it all out.
| Priority | Focus Area | Example | Timeline |
| P0 (Immediate) | Critical & Exploitable | SQL Injection on login page | 24-48 Hours |
| P1 (Urgent) | High-Impact Systems | Missing MFA on admin panels | 7 Days |
| P2 (Scheduled) | Important Improvements | Outdated software on internal servers | 30 Days |
| P3 (Long-term) | Hygiene & Best Practice | Informational findings on headers | Next Quarter |
Turning Findings into a Remediation Plan
Prioritization gives you order, but remediation is the action. This is where many teams stall. The report says “patch the server,” but which team owns it? Who approves the downtime? Effective remediation is a workflow, not a single task.
It starts with triage, a meeting with IT, development, and security to assign every finding an owner, a structure that mirrors how penetration testing coordination keeps vulnerabilities from stalling after discovery.
“Structure your report with different audiences in mind. Offer executive summaries for leadership and detailed technical sections for engineers. This ensures the report speaks effectively to both strategic and operational stakeholders. Use plain language… focus on accessible language that explains each issue clearly.” – Microminder Cyber Security Blog
Then comes implementation. Sometimes it’s a simple patch. Other times, it’s a code rewrite for a web application flaw like cross-site scripting. If a patch isn’t ready, you need a compensating control, like a new Web Application Firewall (WAF) rule to block the attack vector. The key is to never leave a finding in an “open” state without a plan.
Verification is non-negotiable. You must test the fix. Use the exact proof of concept from the report. Can you still trigger the vulnerability? If not, you can close the ticket. For your most critical items, consider a formal retest with your original penetration tester. This provides a clean report for compliance needs like PCI DSS or ISO 27001, and it’s peace of mind.
Building Lasting Security After the Test

A penetration test is a snapshot. The moment the tester stopped, your environment began to change. New code was deployed, a server was configured, a user clicked a phishing link. Interpreting the results isn’t a one-time event, it’s the start of a cycle. The goal is to use the report not as a report card, but as a blueprint for improvement.
Look for patterns. Are half the findings due to misconfigured access control? That points to a process problem, not just a technical one. Use the report to advocate for better training or new security controls. Integrate the specific attack narratives into your threat intelligence. Can your SIEM or SOC now detect the reconnaissance activity the tester used?
This is where a continuous relationship with a partner like MSSP Security helps, turning periodic testing into managed penetration coordination that steadily strengthens your cybersecurity posture over time. It’s about building resilience, not just passing an audit.
The final step is scheduling the next test, often supported through outsourced pen test scheduling that ensures assessments happen consistently without operational delays.
FAQ
How do risk ratings in a penetration test report affect real business decisions?
Risk ratings combine technical severity with business impact to show which security weaknesses matter most. A flaw on public-facing websites handling customer data carries higher risk than the same issue on internal servers.
Understanding CVSS scores and risk level helps teams focus remediation plans where cybersecurity incidents or data breaches are most likely to disrupt operations.
What should I review first when interpreting a penetration testing report?
Start with attack narratives that explain how a penetration tester moved through systems and exploited vulnerabilities. These stories reveal weak access control, outdated software, and exposed attack vectors. Reviewing real exploit paths gives a clearer security snapshot than raw vulnerability lists and shows how cyber attacks could realistically succeed.
How do false positives impact remediation after penetration testing?
False positives waste time and resources by pushing teams to fix issues that don’t actually exist. Security consultants often verify findings using proof of concept exploits across web applications, internal networks, and external networks.
Confirming real vulnerabilities ensures patch management and security controls focus on true risks to your cybersecurity posture.
Why is business impact more important than severity score alone?
A high severity score doesn’t always equal high risk. An SQL injection vulnerability on an online shopping platform affects revenue and compliance requirements like PCI DSS far more than the same flaw on a test server. Interpreting penetration test results means weighing technical risk against impact on business operations.
Your Next Steps with Penetration Test Results
A penetration test report gives you the evidence and the guide. The real work begins when you stop treating it as a document to be filed away and start using it as a plan. Bring it to your team, use it to justify budget, and build a culture that fixes problems before they’re exploited. Your security isn’t about the flaws you find; it’s about what you do next.
Ready to turn findings into a stronger, more efficient security operation? Our team specializes in helping MSSPs streamline their tools and processes, turning technical reports into clear, actionable roadmaps.
References
- https://datcom.com.au/blog/interpret-penetration-test-report
- https://www.micromindercs.com/blog/penetration-testing-report

