ICS incident response planning is the use of the Incident Command System to manage cyber and operational incidents in industrial control environments such as SCADA, PLCs, and critical infrastructure.
In our work supporting utilities and manufacturers, we see that standard IT playbooks break down quickly once physical processes, safety risks, and legacy systems are involved. Decisions affect real-world operations.
Effective ICS planning brings clear command structure, defined roles, and disciplined coordination under stress. This guide explains how ICS applies to cyber incidents in OT and how to build plans that hold up when pressure is high. Keep reading.
Key Takeaways
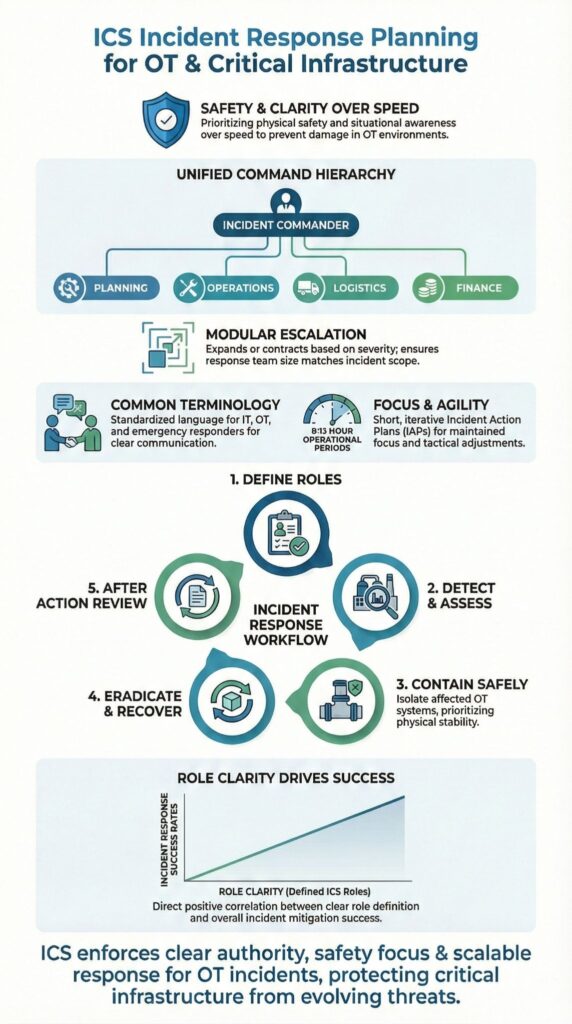
- ICS incident response planning brings clear authority, safety focus, and scalability to OT incidents.
- Simple Incident Action Plans outperform complex documentation during real events.
- Preparation, role clarity, and realistic exercises matter more than tools.
What Is ICS Incident Response Planning?
ICS incident response planning applies the Incident Command System to cyber and operational incidents in industrial control environments. Many MSSPs combine this framework with operational technology OT security monitoring to maintain real-time visibility across OT networks and improve incident response effectiveness.
The ICS framework answers one question: who is in charge, and how does information move. An incident response plan answers a different one: what actions are taken, by whom, and in what order.
In our work supporting MSSPs and asset owners, we see problems when these are treated as the same thing. During escalation, that confusion leads to delays, duplicated effort, and missed decisions.
This distinction matters more in OT than in IT. Downtime can trigger safety risks, environmental impact, or regulatory exposure. We see that structure reduce friction when incidents cross team boundaries.
Key differences teams should anchor early include:
- ICS defines authority, roles, and reporting structure
- Incident response plans define procedures and technical steps
- Both must work together under real operating conditions
When those pieces are aligned, response becomes controlled instead of reactive.
Core ICS Principles That Matter Most for OT

ICS works in industrial environments because it enforces command clarity, prioritizes safety, and allows response structures to grow as incidents evolve. These principles were proven through thousands of emergency responses long before they were adapted for cyber incidents and critical infrastructure.
One principle that matters immediately is clear authority. During a refinery incident we supported, a single commander decision stopped an unsafe PLC restart that could have led to equipment damage and extended downtime. This technical alignment is echoed by experts :
“Industrial control system tabletops will always fall short when engineering is not totally involved throughout the planning and execution of an ICS/OT incident response exercise. Because in any organization that depends on ICS or OT, the operational technology isn’t just part of the business, ICS/OT is the business.” – SANS Institute [1]
Core principles that consistently hold up in OT environments include:
- Unified command when multiple teams or agencies are involved
- Common terminology to prevent misinterpretation under stress
- Modular organization that supports escalation and de-escalation
- Safety officer authority to pause actions that introduce risk
When these principles are applied as designed, response efforts stay controlled even as conditions change.
Incident Action Plans in Practice
An Incident Action Plan turns strategy into clear objectives for a defined operational period, often eight to twelve hours during sustained incidents.
During control system incidents, the focus of an IAP shifts. Safety, containment, and system stabilization come before rapid eradication. We have written IAPs on whiteboards inside temporary command posts when digital systems were unavailable. Those short, visible plans still kept teams aligned and prevented risky actions.
A workable IAP does not need to be polished. What matters is that it captures intent and direction in a way operators can use. In reviews we conduct with MSSPs, we often integrate compliance requirements of OT security under NERC CIP to ensure that operational steps align with regulatory standards while maintaining safety and uptime.
A practical IAP typically includes:
- Clear objectives for the operational period
- Assigned roles and responsibilities
- Communication paths and reporting cadence
- Safety notes and operational constraints
When teams try to over document during an outage, momentum slows. In OT incidents, clarity and speed matter more than completeness.
How ICS Incident Response Planning Changes in OT Environments

OT environments impose limits that change how incident response works in practice. Legacy platforms, vendor-locked controllers, and segmented or air-gapped networks restrict tooling and increase reliance on people and process.
MSSPs often provide advanced specialized services such as tailored OT playbooks and hands-on scenario exercises to address these constraints effectively. In the environments we support, response plans that assume full visibility or rapid patching tend to fail early.
Risk looks different in industrial incidents. Human safety and physical impact often outweigh system uptime. NIST SP 800-82 makes this explicit, safety must take priority over availability during control system incidents.
Collaboration between IT and OT improves when decision rights are clear. We have watched escalations stall because no one was authorized to isolate a Purdue Level 1 zone or pause operations. ICS resolves that tension by assigning authority before incidents occur, not during them.
Key OT-specific adjustments we see teams make include:
- Slower containment that favors stability over speed
- Manual fallback and failover procedures
- Evidence preservation that avoids disrupting operations
When these adjustments are planned upfront, response becomes measured instead of reactive.
ICS Roles and Sections Explained
Credits: SANS ICS Security
ICS divides responsibility so response does not bottleneck around a single leader. Each section has a defined mandate, clear authority, and specific outputs. In OT incidents we support, this structure is often what keeps response efforts moving when pressure builds.
| ICS Section | Primary Responsibility | OT-Specific Focus |
| Incident Command | Overall authority and decision-making | Safety prioritization and operational approval |
| Operations | Execute containment and recovery actions | Field activities, system isolation, safe restart |
| Planning | Develop Incident Action Plans and situation reports | Operational period objectives and demobilization |
| Logistics | Provide resources and access | Tools, credentials, remote access, facilities |
| Finance / Administration | Track costs and compliance | Contract use, regulatory reporting, incident cost tracking |
| Safety Officer | Stop unsafe actions | Human safety and process risk control |
| Liaison Officer | External coordination | Regulators, CISA, sector partners |
| Public Information Officer | Communications | Internal updates and external messaging |
Supporting command staff round out the structure:
- Safety Officer, with authority to stop unsafe actions
- Public Information Officer, managing internal and external messaging
- Liaison Officer, coordinating with groups like CISA and sector regulators
From incidents we have reviewed, response stabilizes faster when each section stays within its role. Overlap feels helpful at first, but it usually creates confusion later.
Common Challenges and How Teams Avoid Them
Role confusion is still the most frequent failure point we see during incident response. When authority is unclear, teams hesitate or work in parallel without alignment. ICS is designed to prevent this, but only if roles are assigned in advance and exercised, not just written down.
Another recurring issue is overreliance on frameworks without enough execution detail. Frameworks help set intent, but they do not tell people what to do at 2 a.m. under pressure. In our reviews with MSSPs, outcomes improve when technical runbooks are mapped directly to ICS roles so responsibility is clear during escalation. As noted in practitioner insights, the technical steps must respect the physical environment:
“The OT version [of a runbook] would add ‘evaluate process state before isolating , if isolating a device will stop a critical process, coordinate with operations for safe shutdown first.’ So while the high-level phases (detect, contain, [etc.]) are the same, it’s wise to have separate appendices or sections in your IR plan for OT scenarios.” – Medium [2]
Teams that avoid these problems tend to focus on a few basics:
- Clear authority and role ownership
- Runbooks that support, not replace, ICS structure
- Exercises that simulate real operating pressure
Those fundamentals matter more than adopting new frameworks.
FAQ
What is ICS incident response planning for industrial and cyber incidents?
ICS incident response planning defines how we prepare for, detect, respond to, and recover from incidents affecting industrial control systems.
We base the incident response plan on the ICS framework, a clear ICS structure, and defined ICS roles. This planning assigns an incident commander, establishes a command post, and uses an incident action plan to manage safety risks and operational impact.
How does the incident command system support OT and cyber incident response?
The incident command system provides a structured and scalable approach for managing OT and cyber incidents. We apply unified command, span of control, and formal escalation procedures to coordinate IT OT convergence.
This structure supports consistent communication, emergency operations center coordination, and effective control during ransomware, SCADA security, or multi-agency incidents.
What key sections should an ICS-based incident response plan include?
An ICS-based incident response plan includes the operations section, planning section, logistics section, and finance section.
We document situation reports, resource status, and an incident action plan using IAP templates and ICS forms. These sections support evidence handling, forensic preservation, safety-first response actions, and compliance-driven reporting requirements.
When should we activate ICS and escalate an incident?
We activate ICS when incidents threaten human safety, disrupt critical infrastructure, or involve PLC compromise or widespread system failure.
We conduct scope assessment, impact analysis, and formal incident declaration early. Clear escalation procedures ensure timely expansion to unified command or MAC group coordination as incident complexity increases.
How do exercises and reviews improve ICS incident response maturity?
ICS exercises validate readiness through tabletop exercises, functional drills, and full-scale simulations. After action reports document lessons learned, response metrics, and performance gaps. We use post-incident reviews to refine playbooks, improve runbook accuracy, strengthen governance frameworks, and advance overall ICS incident response maturity.
ICS Incident Response Planning for Resilient Operations
ICS incident response planning works because it brings clarity, authority, and safety when systems are under stress. In OT environments, those qualities matter more than speed or technical perfection.
The plans that succeed are practical, exercised, and trusted by operators and leadership alike. They reflect real behavior under pressure, not ideal policy assumptions. Build for reality, train often, and adjust as operations change. To align response planning with real OT conditions, schedule a conversation with MSSP Security.
References
- https://www.sans.org/blog/practice-lives-depend-importance-industrial-control-system-incident-response-tabletops
- https://medium.com/@kaoutar.ech.chayeb/incident-response-in-ics-unique-challenges-in-a-factory-cyber-emergency-041d19d86be5
