Watching hackers is like tracking animals in the wild – they leave signs everywhere they go. These signs, or TTPs, tell us their favorite ways to break in, mess around, and steal stuff. Security teams who pay attention to these clues catch the bad guys way before they can do real damage.
It’s not rocket science – it’s just good old detective work applied to computers. Stick around to learn the tricks to understanding threat actor TTPS that’ll help you spot these digital trespassers before they wreck your network.
Key Takeaway
- Reveal attacker behavior patterns to anticipate threats before they strike.
- Build targeted detection and response plans that reduce incident impact.
- Enhance threat intelligence by profiling adversaries and predicting their tactics.
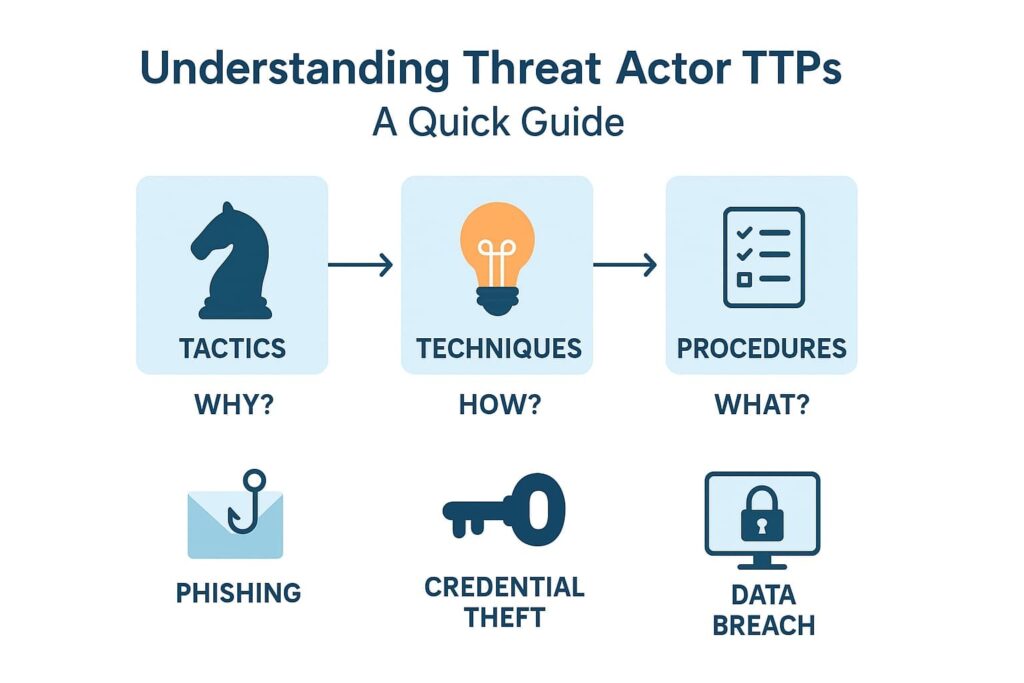
What Are TTPs? Breaking Down the Basics
Most security folks toss around the term TTPs without really getting into the meat of it. Through our years helping MSSPs pick the right tools, we’ve learned that TTPs are really just the recipe book that shows how attackers cook up trouble.
Tactics: The “Why” Behind an Attack
Security teams spot tactics first – they’re the big-picture goals driving an attack. After auditing hundreds of incidents, we’ve narrowed down the main reasons attackers strike:
- Data Exfiltration – swiping anything valuable
- Credential Theft – stealing keys to the kingdom
- Service Disruption – throwing wrenches in the works
Take last month’s case: our client faced an attacker who deliberately hit their payment system during Black Friday. Classic disruption tactic.
Techniques: The “How” of the Attack
The nitty-gritty methods attackers use make up their techniques. These aren’t just theoretical – we see them in action daily:
- Phishing – sweet-talking folks into giving up passwords
- Malware Drops – sneaking in nasty code
- Vulnerability Hunting – poking holes in weak spots
Here’s the kicker – attackers mix and match these techniques. When helping MSSPs track data theft, we often catch bad guys using both sneaky command channels and encrypted messages to avoid getting caught. [1]
Procedures: The “What” That Happens Step-by-Step
Down in the trenches, procedures show exactly how attackers pull off their tricks. Our incident response team watches these digital fingerprints daily – they’re like a criminal’s step-by-step cookbook.
Through years of helping MSSPs catch bad guys, we’ve documented the most common moves:
- Crafting fake emails that could fool even tech-savvy users
- Breaking into networks using tools like CrackMapExec (nasty piece of work)
- Running bot armies to flood servers until they crash
Each crook has their own style. Last week, we caught one group using custom Python scripts for their attacks, while another stuck to off-the-shelf hacking tools. These little details help MSSPs figure out who’s behind each attack – sort of like catching bank robbers by their methods.
Why TTPs Are Game-Changers in Cybersecurity
Credit: CBT nuggets
We’ve worked alongside many organizations that struggled with endless alerts and slow incident response. Shifting focus to TTPs changed the game. Here’s why:
Proactive Threat Detection
When you understand attacker patterns, you can spot anomalies early. Instead of chasing alerts blindly, you’re hunting behaviors that match known adversary playbooks, allowing you to anticipate attacks before impact.
Improved Incident Response
Knowing the “how” and “what” behind attacks enables your team to craft targeted detection rules and response plans. This focus on behavior patterns plays a major role in reducing threat detection time, resulting in faster containment, less damage, and a smoother recovery process.
Enhanced Threat Intelligence
Profiling threat actors through their TTPs helps predict their next moves and motivations. This kind of insight is central to building stronger threat intelligence service that arms your defenses and informs strategic decisions, from patch management to user training.
Using TTPs to Strengthen Your Security Posture

In practice, integrating TTP awareness into daily operations is vital. Here are some proven ways:
Threat Hunting
We regularly use TTP-based indicators to proactively search for hidden threats lurking in networks. By combining this approach with industry-specific threat feeds, threat hunting becomes more effective and precise, helping analysts focus on relevant attacker patterns.
Vulnerability Management
Understanding which TTPs exploit certain vulnerabilities helps prioritize patching efforts. This reduces your attack surface by focusing on weaknesses attackers are most likely to target. [2]
Security Controls Implementation
Deploying intrusion detection and prevention systems tuned to known TTPs improves your ability to block attacks. Enforcing strict access controls and application whitelisting also closes doors that attackers use frequently.
Employee Training
Educating users about common TTPs, like phishing and social engineering tactics, builds a human firewall. A security-aware workforce is one less easy target for attackers.
Real-World Examples of Threat Actor TTPs
Seeing TTPs in action clarifies their value.
Example 1: Ransomware Attack
| Tactic | Technique | Procedure |
| Data Encryption & Extortion | Malware Deployment (Ransomware) | Phishing email with malicious attachment sent, user executes ransomware, files encrypted, ransom demanded |
The attacker’s goal (tactic) is to encrypt data for extortion. They use malware deployment (technique) via phishing (procedure) to initiate the attack.
Example 2: Data Breach
| Tactic | Technique | Procedure |
| Data Exfiltration | Credential Theft | Spear-phishing email targets employees, fake login page captures credentials, attacker accesses and steals data |
This shows how attackers combine social engineering with credential theft to steal sensitive information.
Frameworks and Resources to Map TTPs
Many organizations rely on established frameworks to structure their understanding of TTPs.
MITRE ATT&CK Framework
This is a comprehensive, evolving knowledge base that categorizes tactics, techniques, and procedures based on real-world observations. It empowers security teams to identify specific adversary behaviors and tailor defenses accordingly.
Cyber Kill Chain
The Cyber Kill Chain breaks down the stages of an attack from reconnaissance to final objectives, helping defenders map out and interrupt attacker progress.
Other Resources
Open Web Application Security Project (OWASP) and Cyber Threat Alliance offer valuable threat intelligence and best practices aligned with TTP concepts.
Tools for TTP Identification and Tracking

Leveraging the right tools is crucial for operationalizing TTP knowledge.
- Security Information and Event Management (SIEM) systems consolidate logs and detect suspicious patterns.
- Endpoint Detection and Response (EDR) monitors device activity in real time.
- Threat Intelligence Platforms (TIP) aggregate and analyze data to correlate events with known TTPs.
From our experience, integrating these tools with MSSP Security services can enhance detection and response capabilities while freeing up internal resources.
Understanding TTPs in Cloud Environments
The cloud adds unique challenges. Attackers exploit misconfigured storage, overly permissive identity policies, and vulnerable APIs. Applying TTP knowledge here means focusing on cloud-specific attack vectors and adjusting defenses to ephemeral and multi-cloud architectures.
FAQ
1. What are threat actor TTPs and why do they matter in cybersecurity?
Threat actor TTPs, or tactics, techniques, and procedures, describe how attackers plan and carry out cyber attack methods. They include everything from reconnaissance techniques to privilege escalation methods.
Understanding these attacker methodologies helps improve threat intelligence, threat hunting, and incident response, making it easier to predict and stop future attacks.
2. How do threat actor tactics and techniques evolve over time?
Threat actor tactics constantly change as cyber adversaries learn from detection engineering and update their attack procedures. New cyber threat techniques like zero-day exploitation and social engineering tactics appear often.
Studying the cyber attack lifecycle through frameworks such as the MITRE ATT&CK framework helps analysts track adversary behavior and adapt cyber defense strategies effectively.
3. What’s the link between the cyber kill chain and threat actor TTPs?
The cyber kill chain outlines each attack stage, from initial access tactics to data exfiltration tactics. Threat actor TTPs map directly to these steps, showing how cyber threat actors move through the system using persistence techniques or lateral movement tactics.
Understanding this attack timeline helps teams improve intrusion detection and incident mitigation.
4. How can understanding threat actor profiling improve cyber defense?
Threat actor profiling combines threat intelligence and threat modeling to identify adversary behavior and attack motivations. By studying specific cyber threat actor groups and their attack vectors, security teams can predict likely breach tactics and apply the right security controls.
This proactive approach supports stronger SOC operations and better cyber risk management.
Conclusion
We’ve learned that TTPs are more than just jargon, they’re the lens through which we understand and anticipate cyber threats. By dissecting the why, how, and what of attacker behavior, security teams can design smarter defenses, respond faster, and minimize risks.
For organizations looking to elevate their cybersecurity strategy, partnering with an MSSP Security provider can be the first step. With expert support focused on TTP detection and response, you can stay ahead in this relentless battle.
Want to bring deeper TTP insights into your security operations? We’re here to help.
References
- https://en.wikipedia.org/wiki/Threat_actor
- https://www.ibm.com/think/topics/threat-actor
